Tim Blazytko and Moritz Contag
Do you want to learn how modern binary code obfuscation and deobfuscation works? Did you ever encounter road-blocks where well-known deobfuscation techniques do not work? Do you want to see a novel deobfuscation method that learns the code's behavior without analyzing the code itself? Then come to our talk and we give you a step-by-step guide.
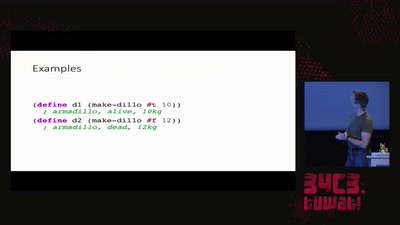
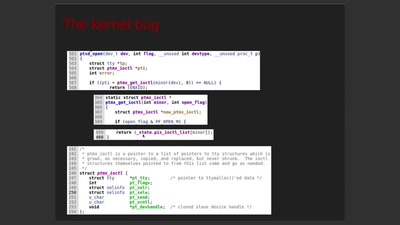
This talk might be interesting for you if you love reverse engineering or binary security analysis. We present you modern code obfuscation techniques, such as opaque predicates, arithmetic encoding and virtualization-based obfuscation. Further, we explain state-of-the-art methods in (automated) deobfuscation [1] as well as how to break these [2]. Finally, we introduce a novel approach [3] that learns the code's semantics and demonstrate how this can be used to deobfuscate real-world obfuscated code.
[1] https://www.ieee-security.org/TC/SP2015/papers-archived/6949a674.pdf
[2] https://mediatum.ub.tum.de/doc/1343173/1343173.pdf
[3] https://www.usenix.org/system/files/conference/usenixsecurity17/sec17-blazytko.pdf
Download
Video
These files contain multiple languages.
This Talk was translated into multiple languages. The files available for download contain all languages as separate audio-tracks. Most desktop video players allow you to choose between them.
Please look for "audio tracks" in your desktop video player.