Search for "Ari" returned 5363 results
58 min
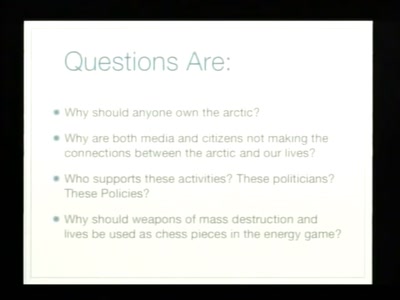
The Arctic Cold War
The silent battle for claiming and controlling the Arctic
63 min
Malware Joe Blobs
An overview of stuff that "Malware Joe" puts into his…
29 min
AppArmor 3 and beyond
riding the Tumbleweed
66 min
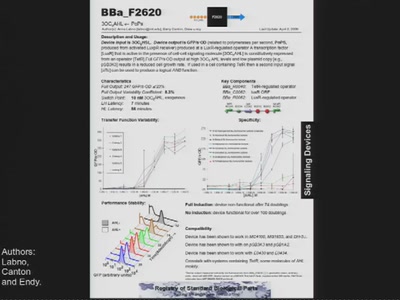
Hacking DNA
Compiling code for living systems
31 min
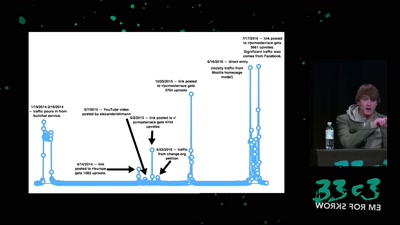
Make the Internet Neutral Again
Let's put the new EU Net Neutrality rules to work

32 min
Cryptokids
empower kids and provide tools for them to be more secure…

61 min
The Invisible Committee Returns with "Fuck Off Google"
Cybernetics, Anti-Terrorism, and the ongoing case against…
53 min
Cryptography demystified
An introduction without maths
38 min
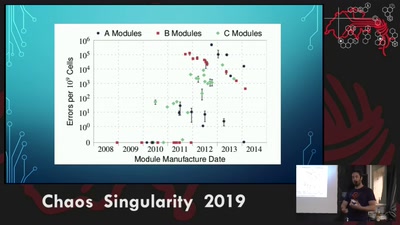
Rowhammer exploit
Viability of the Rowhammer Attack when ECC memory is used

65 min
There's Gold in Them Circuit Boards
Why E-Waste Recycling Is Smart and How To Make It Smarter
53 min