Search for "AKO" returned 1184 results
38 min
A deep dive into the world of DOS viruses
Explaining in detail just how those little COM files…
45 min
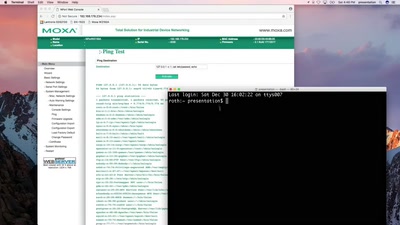
SCADA - Gateway to (s)hell
Hacking industrial control gateways
29 min
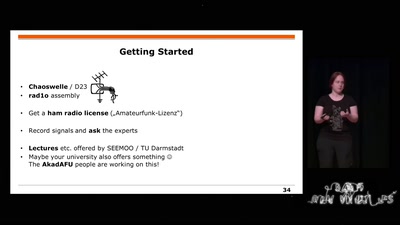
Building and Breaking Wireless Security
Wireless Physical Layer Security & More...
66 min
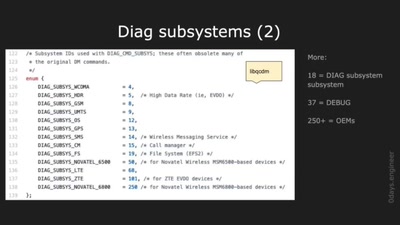
Advanced Hexagon Diag
Harnessing diagnostics for baseband vulnerability research
58 min
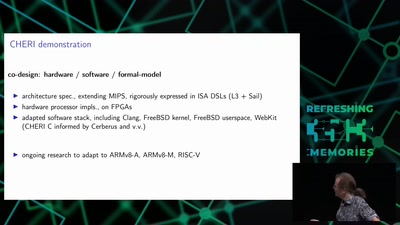
Taming the Chaos: Can we build systems that actually work?
Possible paths from today's ghastly hackery to what…
61 min
Nintendo Hacking 2016
Game Over
32 min
History and implications of DRM
From tractors to Web standards

59 min
Security of the IC Backside
The future of IC analysis
59 min
Fernvale: An Open Hardware and Software Platform, Based on the (nominally) Closed-Source…
A Lawful Method for Converting Closed IP into Open IP
60 min
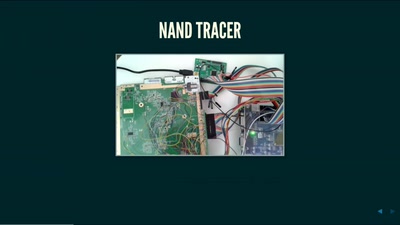
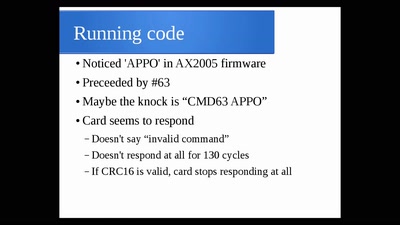
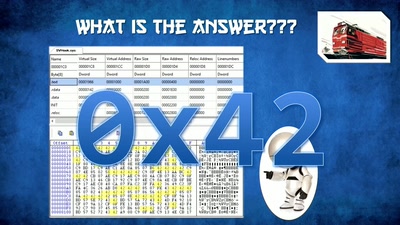
The Exploration and Exploitation of an SD Memory Card
by xobs & bunnie
52 min
SiliVaccine: North Korea's Weapon of Mass Detection
How I Learned to Stop Worrying and Love the Backdoor
29 min
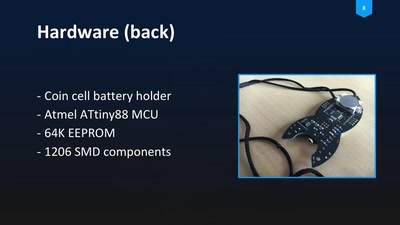
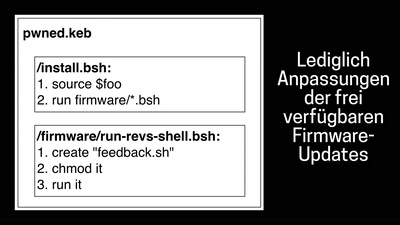
Blinkenrocket!
How to make a community project fly
52 min
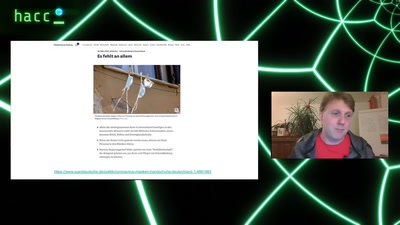
Ladeinfrastruktur für Elektroautos: Ausbau statt Sicherheit
Warum das Laden eines Elektroautos unsicher ist

33 min