Search for "sECuRE"
prev
next
59 min
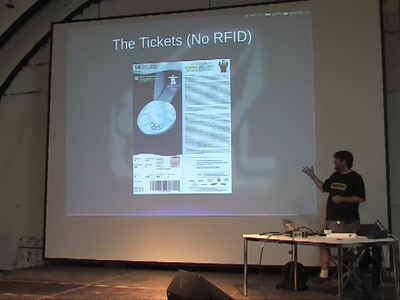
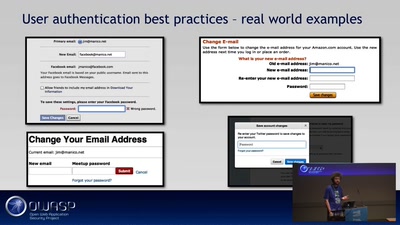
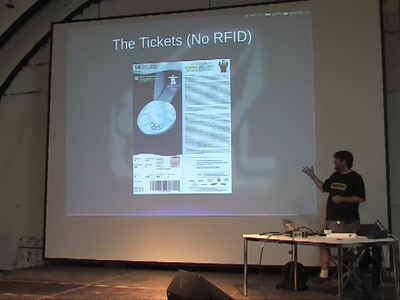
Little Security, Despite Obscurity
69 min
Sichere Anwendungen erstellen?
63 min
The 7 Laws of Identity and the Identity Metasystem
51 min
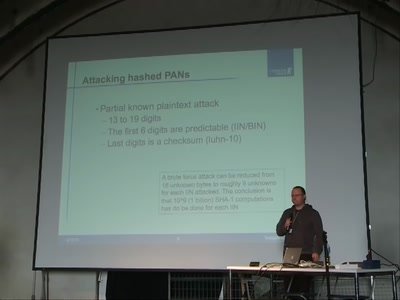
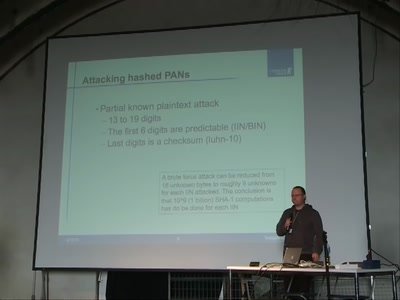
Attacks on common failures when encrypting credit card…
54 min
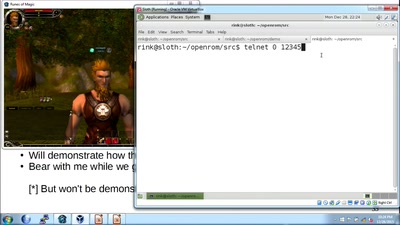
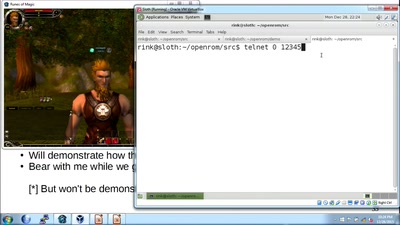
An introduction to reverse engineering network protocols

59 min
The future of IC analysis
46 min
Social Networks, Free Speech and the Criminalization of…
26 min
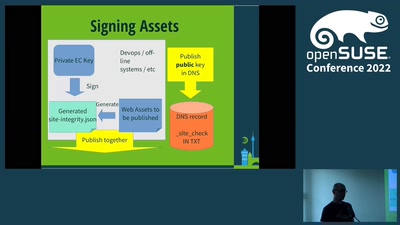
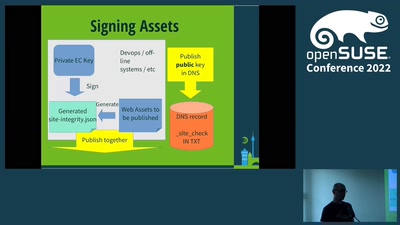
and how to verify that Javascript before you trust your…

47 min
Learn about the building blocks of a network application
prev
next