Search for "John" returned 1058 results

60 min
Attacking end-to-end email encryption
Efail, other attacks and lessons learned.
63 min
Reconstructing narratives
transparency in the service of justice
63 min
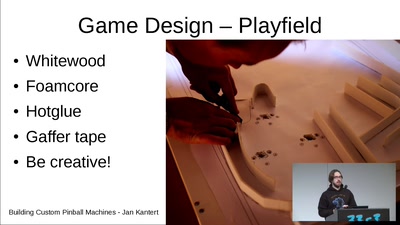
Building Custom Pinball Machines
What you need and how it works. An experiences report

61 min
The Invisible Committee Returns with "Fuck Off Google"
Cybernetics, Anti-Terrorism, and the ongoing case against…
61 min
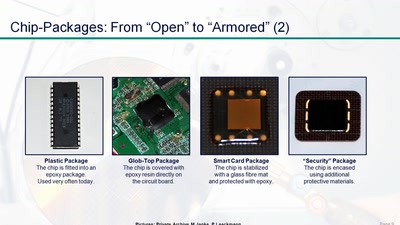
Uncaging Microchips
Techniques for Chip Preparation

32 min
Verified Firewall Ruleset Verification
Math, Functional Programming, Theorem Proving, and an…

66 min
Mit, gegen oder jenseits von Politik?
Eine Reflexion über den paradoxen anarchistischen…
58 min
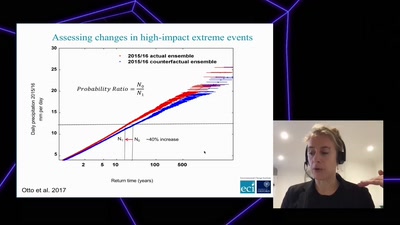
Angry weather ?
How human-induced climate change affects weather (& how we…
52 min
SiliVaccine: North Korea's Weapon of Mass Detection
How I Learned to Stop Worrying and Love the Backdoor
47 min
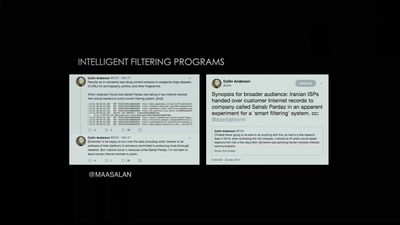
Tightening the Net in Iran
The Situation of Censorship and Surveillance in Iran, and…
32 min
Eye Wear Computing
Augmenting the Human Mind
62 min
Transhuman Expression
Interdisciplinary research in Painting and Robotics. with…
64 min
3 Years After Snowden: Is Germany fighting State Surveillance?
A Closer Look at the Political Reactions to Mass…
62 min
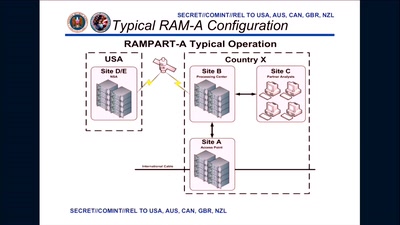
Tell no-one
A century of secret deals between the NSA and the telecom…

58 min
Funkzellenabfrage: Die alltägliche Rasterfahndung unserer Handydaten
Wie wir alle regelmäßig den Behörden ins Netz gehen und wie…
55 min
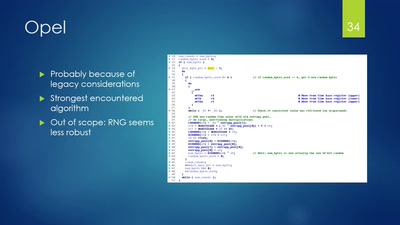
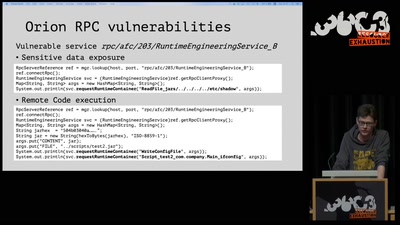
Vehicle immobilization revisited
Uncovering and assessing a second authentication mechanism…
60 min
On the insecure nature of turbine control systems in power generation
A security study of turbine control systems in power…
53 min
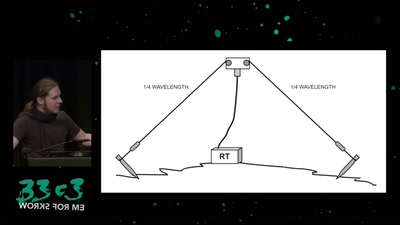
Surveilling the surveillers
About military RF communication surveillance and other…

60 min