Search for "Saud Al-Zaid" returned 1117 results
40 min
Never Forgetti
a didactic live-gaming performance about dying women across…
61 min
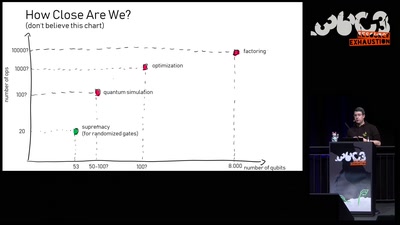
Quantum Computing: Are we there yet?
An introduction to quantum computing and a review of the…

60 min
Free Software and Hardware bring National Sovereignty
Gaza as a case study

61 min
AlphaFold – how machine learning changed structural biology forever (or not?)
Getting first-hand insights into the impact of machine…
62 min
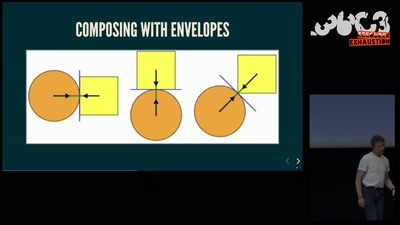
Getting software right with properties, generated tests, and proofs
Evolve your hack into robust software!

32 min
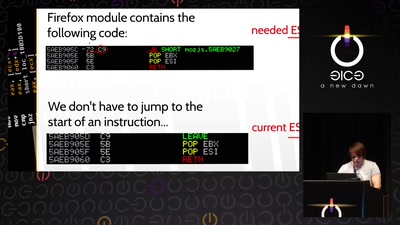
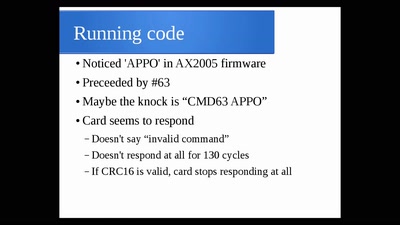
Finding the Weak Crypto Needle in a Byte Haystack
Automatic detection of key-reuse vulnerabilities
59 min
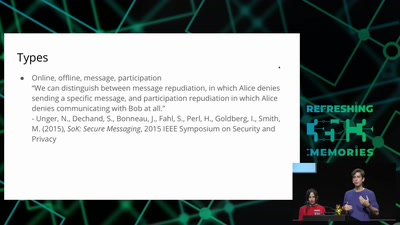
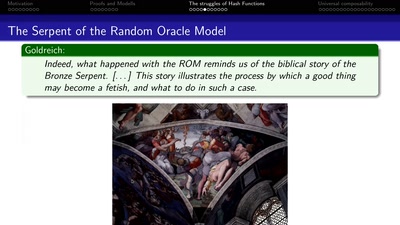
Provable Security
How I learned to stop worrying and love the backdoor
58 min
Hack_Curio
Decoding The Cultures of Hacking One Video at a Time
32 min
Think big or care for yourself
On the obstacles to think of emergent technologies in the…
59 min
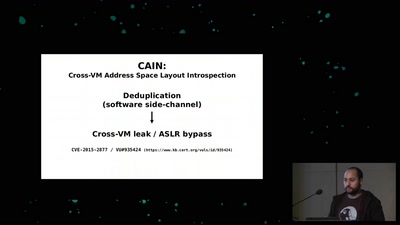
Memory Deduplication: The Curse that Keeps on Giving
A tale of 3 different memory deduplication based…
64 min
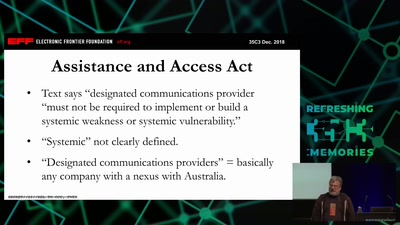
It Always Feels Like the Five Eyes Are Watching You
Five Eyes’ Quest For Security Has Given Us Widespread…
33 min
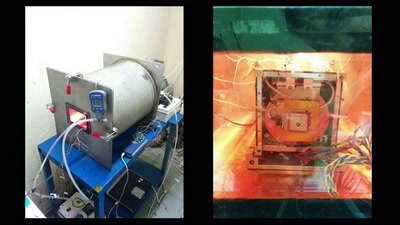
UPSat - the first open source satellite
Going to space the libre way
60 min