eng
Help us to improve these subtitles!
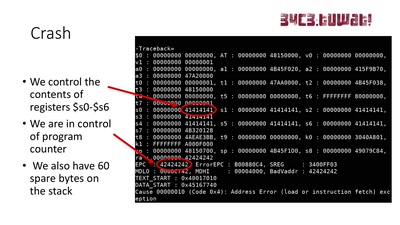
This talk presents the technical details and the process of reverse engineering and re-implementation of the evasi0n7 jailbreak's main kernel exploit. This work was done in late 2013, early 2014 (hence the "archaeology" in the title), however, it will provide insight into the kernel debugging setup for iOS devices (iDevices), the encountered difficulties and how they were overcome, all of which can be useful for current iOS kernel vulnerability research.
Download
Video
These files contain multiple languages.
This Talk was translated into multiple languages. The files available for download contain all languages as separate audio-tracks. Most desktop video players allow you to choose between them.
Please look for "audio tracks" in your desktop video player.