Search for "Ari" returned 5383 results
30 min
Automatically Subtitling the C3
How speech processing helps the CCC subtitle project, and…
61 min
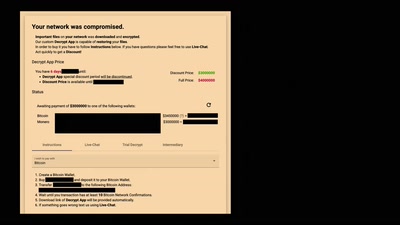
Hirne hacken: Hackback Edition
Wir verhandeln mit Erpressern, damit Ihr es nicht müsst.
41 min
MicroPython – Python for Microcontrollers
How high-level scripting languages make your hardware…
46 min
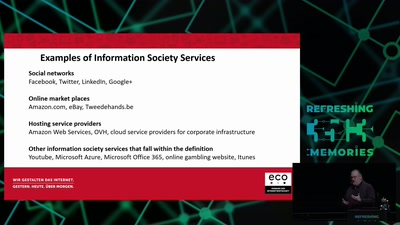
Electronic Evicence in Criminal Matters
An introduction and critique of the EC proposal for a…
33 min
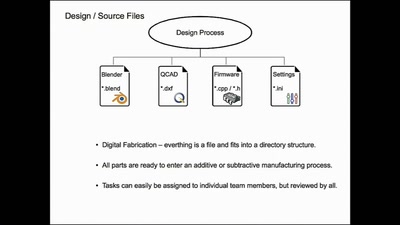
Structuring open hardware projects
experiences from the “i3 Berlin” 3D printer project with…
45 min
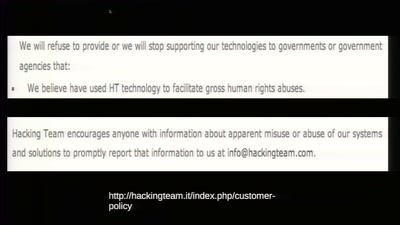
To Protect And Infect
The militarization of the Internet
60 min
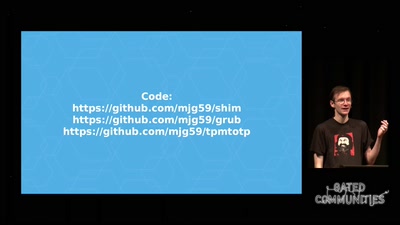
Beyond Anti Evil Maid
Making it easier to avoid low-level compromise, and why…

58 min
The Magic World of Searchable Symmetric Encryption
A brief introduction to search over encrypted data
32 min
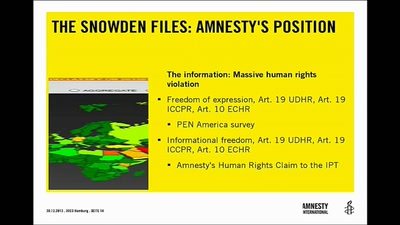
Human Rights and Technology
"A New Hope" or "The Empire Strikes Back"?

41 min
Extracting keys from FPGAs, OTP Tokens and Door Locks
Side-Channel (and other) Attacks in Practice
32 min
The Case for Scale in Cyber Security
Security Track Keynote
30 min
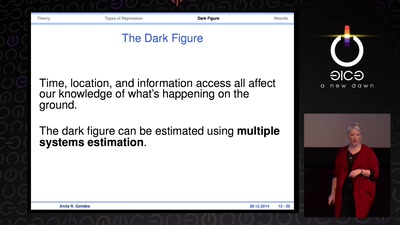
Information Control and Strategic Violence
How governments use censorship and surveillance as part of…
30 min
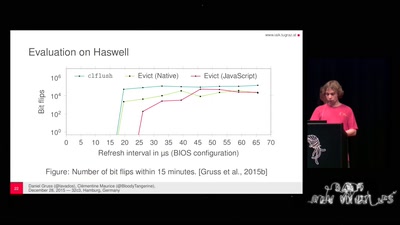
Rowhammer.js: Root privileges for web apps?
A tale of fault attacks on DRAM and attacks on CPU caches

45 min