Search for "zem" returned 4276 results
47 min
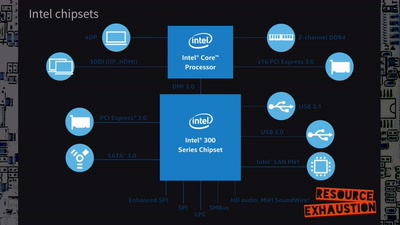
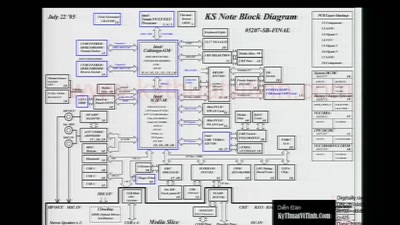
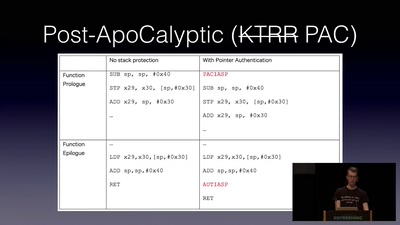
Hardening hardware and choosing a #goodBIOS
Clean boot every boot - rejecting persistence of malicious…
46 min
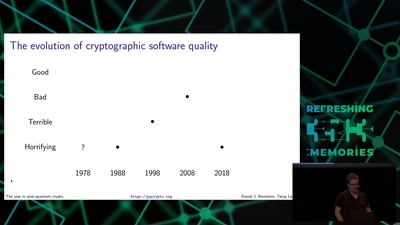
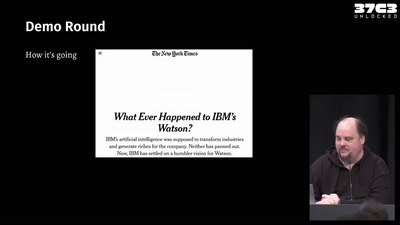
Writing secure software
using my blog as example
59 min
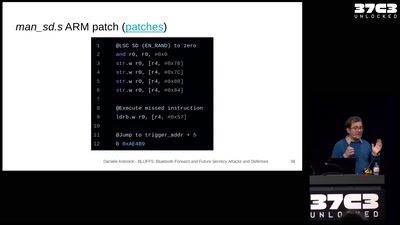
BLUFFS: Bluetooth Forward and Future Secrecy Attacks and Defenses
Breaking and fixing the Bluetooth standard. One More Time.
61 min
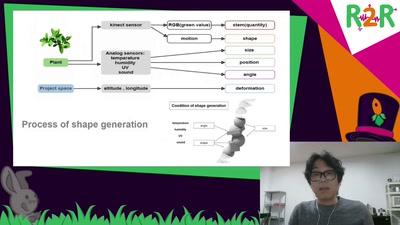
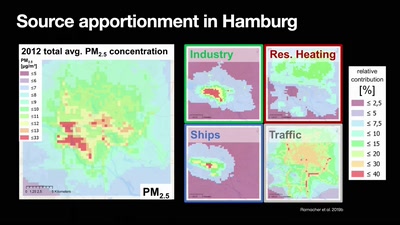
Numerical Air Quality Modeling Systems
a journey from emissions to exposure
55 min
YOU’VE JUST BEEN FUCKED BY PSYOPS
UFOS, MAGIC, MIND CONTROL, ELECTRONIC WARFARE, AI, AND THE…
65 min
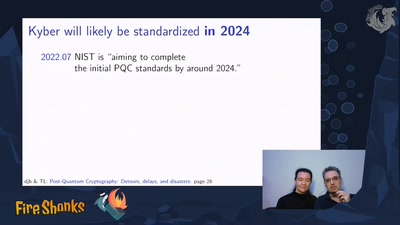
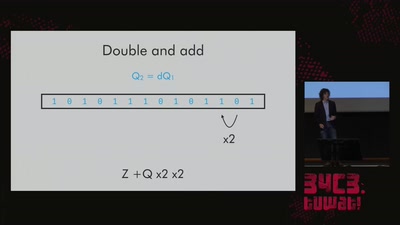
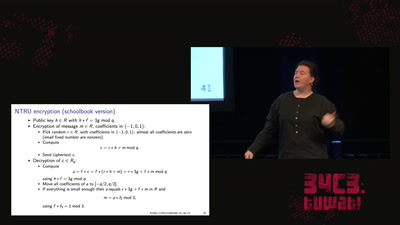
LatticeHacks
Fun with lattices in cryptography and cryptanalysis
71 min
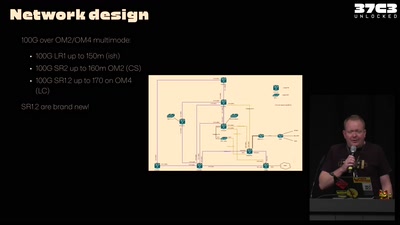
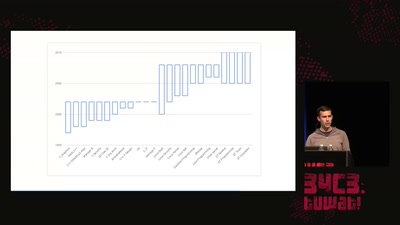
37C3 Infrastructure Review
Teams presenting how they helped making this awesome event

60 min
HAL - The Open-Source Hardware Analyzer
A dive into the foundations of hardware reverse engineering…
31 min
DPRK Consumer Technology
Facts to fight lore
49 min
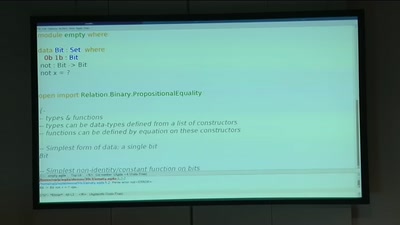
BREACH in Agda
Security notions, proofs and attacks using dependently…
38 min
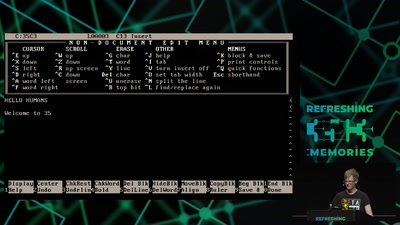
A deep dive into the world of DOS viruses
Explaining in detail just how those little COM files…
47 min