Search for "Max" returned 4737 results
41 min
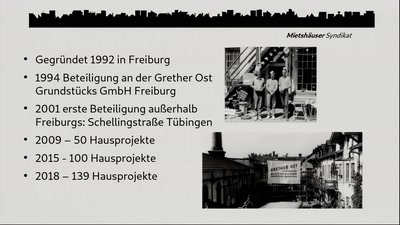
Die Häuser denen, die darin wohnen!
Langfristig bezahlbares, gemeinsames „Mieteigentum“…
64 min
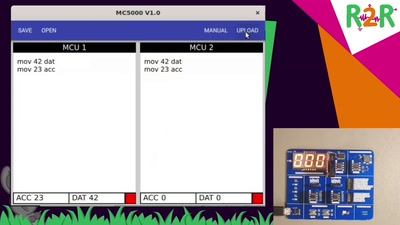
ES GIBT VIEL ZU TUN - HAU'N WIR AB.
[Die Untersuchung]
29 min
2 Takte später
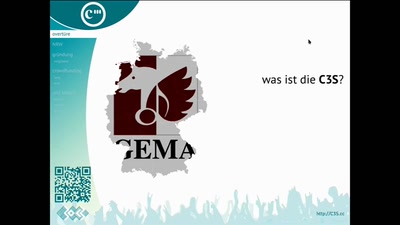
30C3S SCE mbH: GEMA-Konkurrenz für Fortgeschrittene
63 min
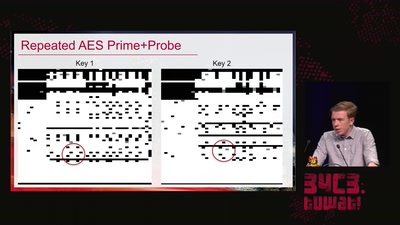
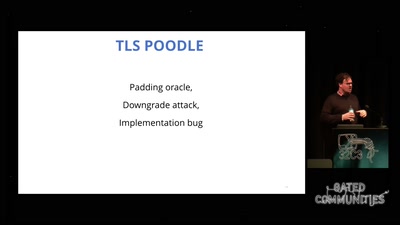
goto fail;
exploring two decades of transport layer insecurity

37 min
Wie der kleine Basti die Welt erobern wollte und was dabei schiefging. Eine Moritat aus…
"Es wird nicht ohne hässliche Bilder gehen"
41 min
Archäologische Studien im Datenmüll
Welche Daten speichert Amazon über uns?
60 min