Search for "c-atre" returned 3750 results

45 min
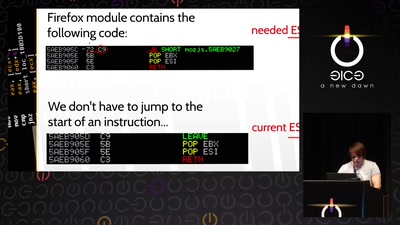
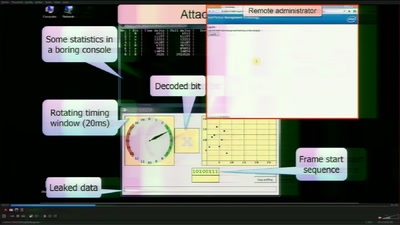
Triggering Deep Vulnerabilities Using Symbolic Execution
Deep program analysis without the headache
46 min
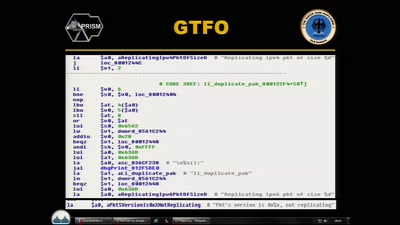
CounterStrike
Lawful Interception

54 min
What Price the Upload Filter?
The history and costs of government exceptional access
55 min
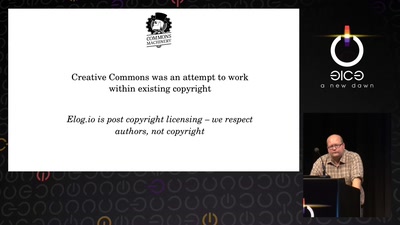
Attribution revolution
Turning copyright upside-down with metadata
63 min
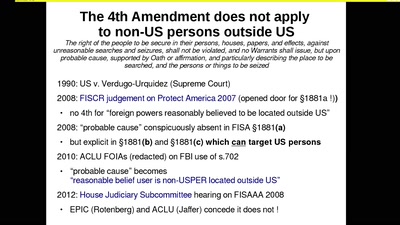
The Cloud Conspiracy 2008-2014
how the EU was hypnotised that the NSA did not exist
54 min
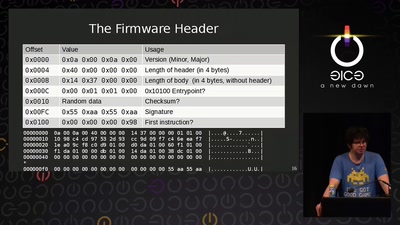
AMD x86 SMU firmware analysis
Do you care about Matroshka processors?
55 min
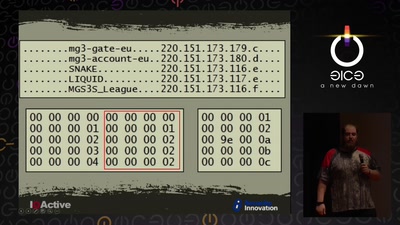
Cyber Necromancy
Reverse Engineering Dead Protocols
30 min
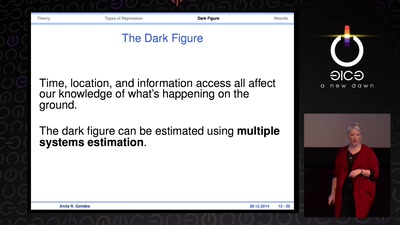
Information Control and Strategic Violence
How governments use censorship and surveillance as part of…
63 min
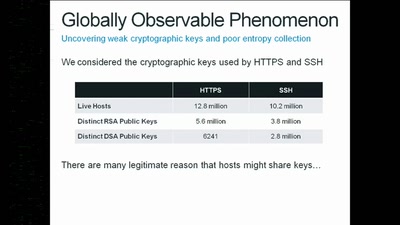
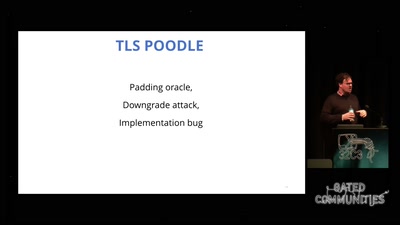
goto fail;
exploring two decades of transport layer insecurity
60 min
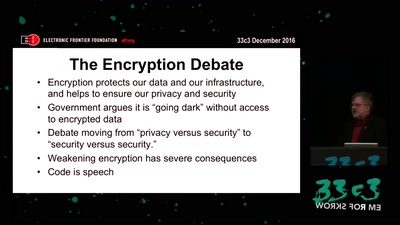
The Fight for Encryption in 2016
Crypto fight in the Wake of Apple v. FBI
61 min
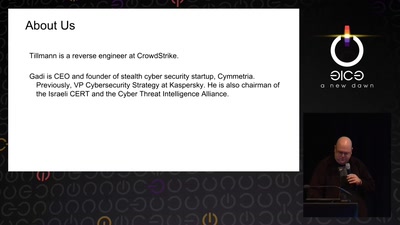
Rocket Kitten: Advanced Off-the-Shelf Targeted Attacks Against Nation States
A Deep Technical Analysis
48 min