Search for "tor" returned 10373 results
27 min
*sing* %post and %pre and securiteeee
How not to get a CVE assigned while packaging
29 min
What de.fac2?
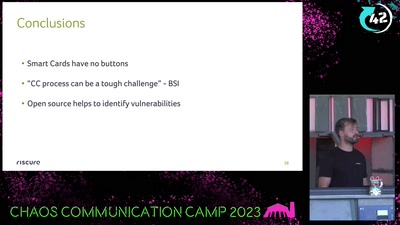
Attacking an opensource U2F device in 30 minutes or less
36 min
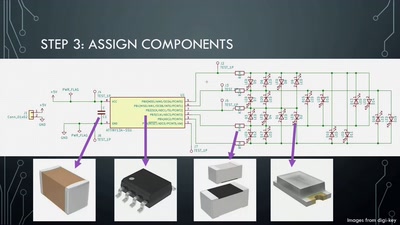
Artistic PCB Design and Fabrication
From doodle to manufacture: how I make mechanically…
49 min
Mining Search Queries
How to discover additional knowledge in the AOL query logs

53 min
Know your compiler
...and what the optimizer does so you don't have to
61 min
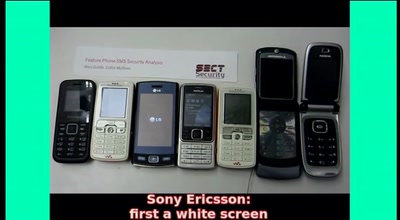
SMS-o-Death
From analyzing to attacking mobile phones on a large scale.

60 min
the possibility of an army
phone verified accounts bringing the Hessian army back to…

30 min
Mobile devices and openSUSE, is it posible?
It is time to check if we can use a mobile device with a…
28 min
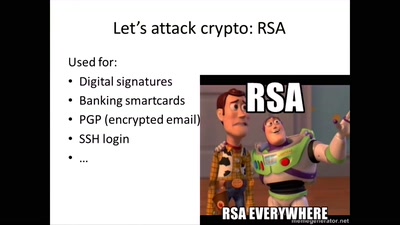
Hardware attacks: hacking chips on the (very) cheap
How to retrieve secret keys without going bankrupt

31 min
Demystifying Network Cards
Things you always wanted to know about NIC drivers
40 min
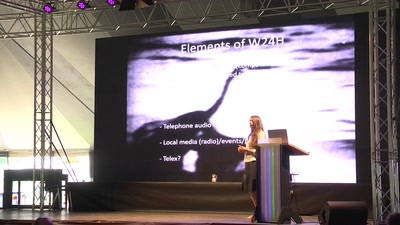
The World in 24 Hours Revisited
How to re-enact a 1982 network art performance
29 min
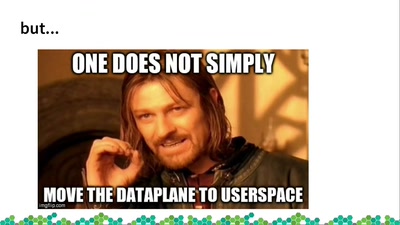
Open vSwitch and DPDK - Your VMs deserve better
Using OvS + DPDK to boost inter-VM network traffic

59 min
10GE monitoring live!
How to find that special one out of millions
53 min
Crouching Powerpoint, Hidden Trojan
An analysis of targeted attacks from 2005 to 2007
43 min
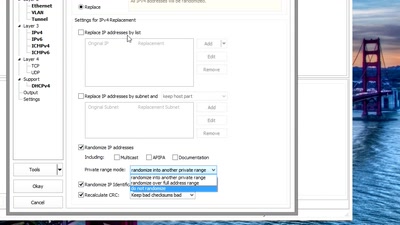
Sanitizing PCAPs
Fun and games until someone uses IPv6 or TCP
37 min
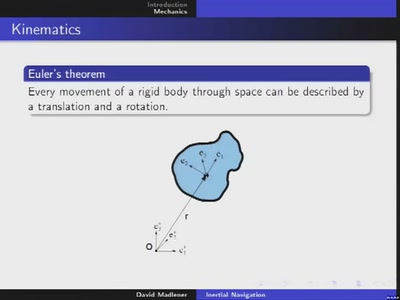
Inertial navigation
Rigid body dynamics and its application to dead reckoning
61 min
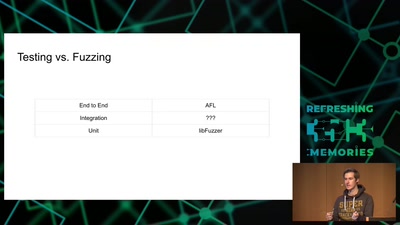
Code Pointer Integrity
... or how we battle the daemons of memory safety
54 min
Attacking Chrome IPC
Reliably finding bugs to escape the Chrome sandbox
43 min
Artist Talk
We Show You What You Want To See
35 min
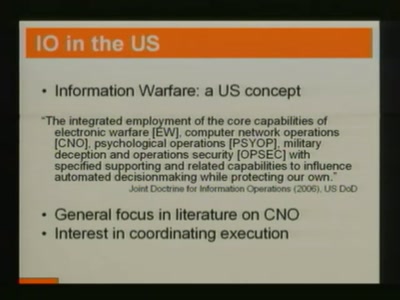
Weaponized Social
Understanding and tools to mitigate network-scale violences

41 min
MySQL Plugins - what are they ?
how can you use them to do wonders
29 min
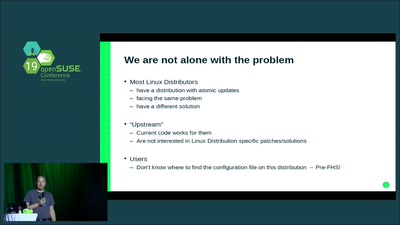
Atomic Updates - and /etc?
How to handle updates of config files in /etc
37 min