Search for "16" returned 4650 results

62 min
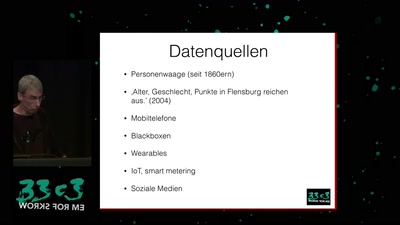
Corporate surveillance, digital tracking, big data & privacy
How thousands of companies are profiling, categorizing,…
49 min
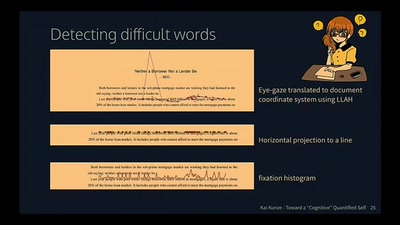
Toward a Cognitive "Quantified Self"
Activity Recognition for the Mind
51 min
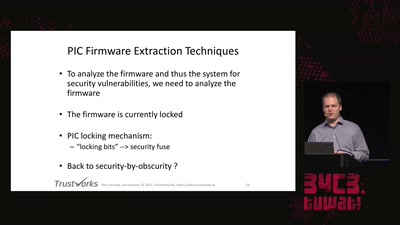
Uncovering vulnerabilities in Hoermann BiSecur
An AES encrypted radio system
63 min
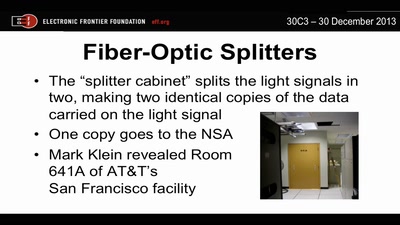
Through a PRISM, Darkly
Everything we know about NSA spying
51 min
Ecuador: how an authoritarian government is fooling the entire world
Guess what? The Government of Rafael Correa actually is…
58 min
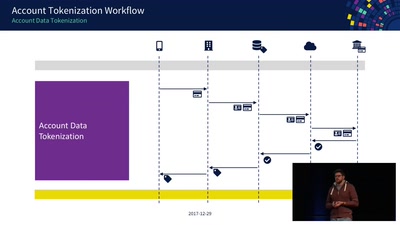
Decoding Contactless (Card) Payments
An Exploration of NFC Transactions and Explanation How…
59 min
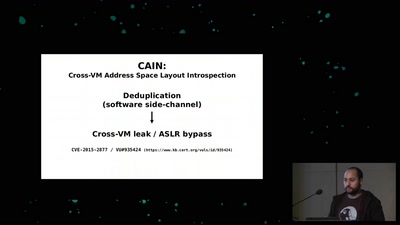
Memory Deduplication: The Curse that Keeps on Giving
A tale of 3 different memory deduplication based…
58 min
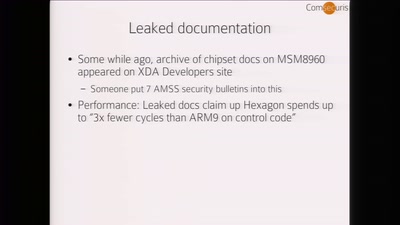
Baseband Exploitation in 2013
Hexagon challenges
58 min
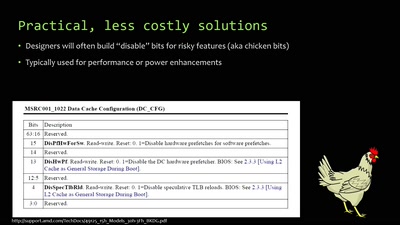
When hardware must „just work“
An inside look at x86 CPU design
60 min
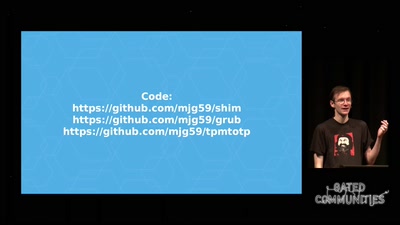
Beyond Anti Evil Maid
Making it easier to avoid low-level compromise, and why…

58 min
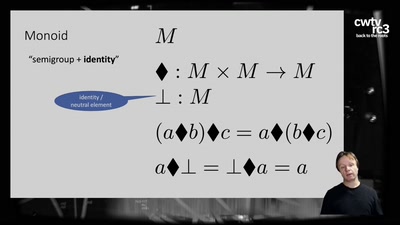
The Magic World of Searchable Symmetric Encryption
A brief introduction to search over encrypted data
60 min
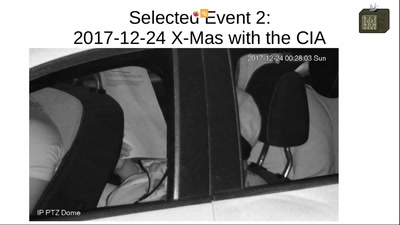
Concepts for global TSCM
getting out of surveillance state mode
57 min
![Why we are addicted to lithium [1/2]](https://static.media.ccc.de/media/events/rc3/2021/193-3fd1b8af-9ab6-54c5-88ad-2622c1cc925a.jpg)