Search for "13" returned 4826 results
60 min
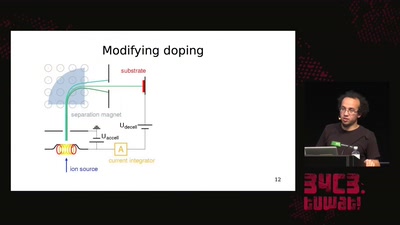
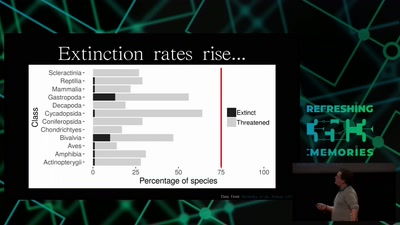
Hacking Ecology
How Data Scientists can help to avoid a sixth global…

60 min
Are machines feminine?
exploring the relations between design and perception of…

60 min
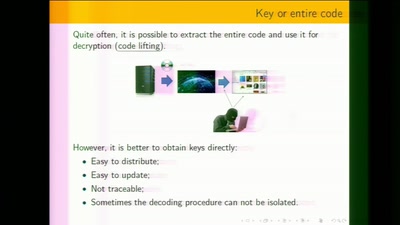
Attacking end-to-end email encryption
Efail, other attacks and lessons learned.
41 min
NGI Zero: A treasure trove of IT innovation
Resilient. Trustworthy. Sustainably Open.
58 min
Hacking how we see
A way to fix lazy eye?
25 min
Keys of Fury
Type In Beyond the Scrolling Horizon
30 min
The ArduGuitar
An Arduino Powered Electric Guitar
58 min
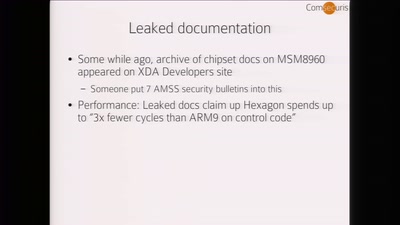
Baseband Exploitation in 2013
Hexagon challenges
49 min
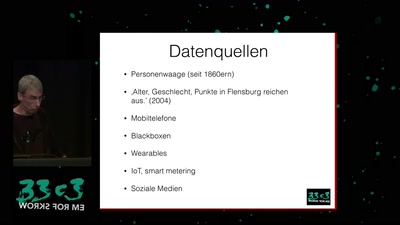
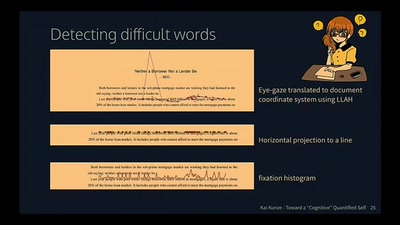
Toward a Cognitive "Quantified Self"
Activity Recognition for the Mind
51 min
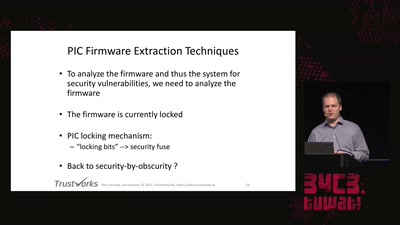
Uncovering vulnerabilities in Hoermann BiSecur
An AES encrypted radio system

117 min
Fnord News Show
Wir helfen Euch die Fnords zu sehen.
51 min
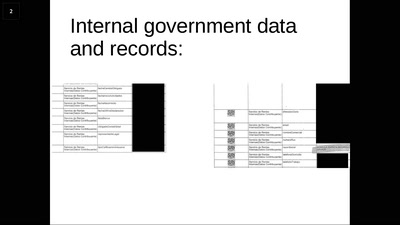
Ecuador: how an authoritarian government is fooling the entire world
Guess what? The Government of Rafael Correa actually is…

60 min
Hacking Reality
Mixed Reality and multi-sensory communication
59 min
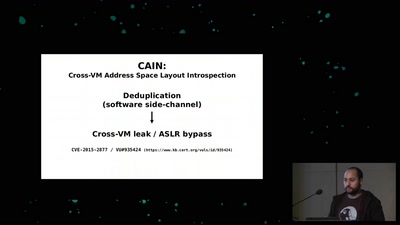
Memory Deduplication: The Curse that Keeps on Giving
A tale of 3 different memory deduplication based…
58 min
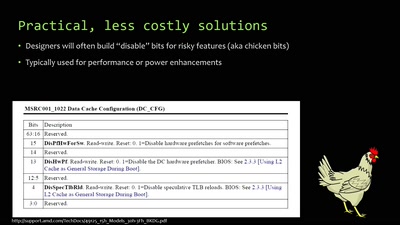
When hardware must „just work“
An inside look at x86 CPU design
55 min