Search for "fake" returned 2878 results
60 min
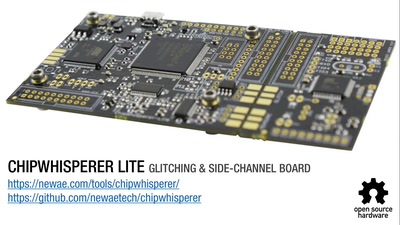
Opening Closed Systems with GlitchKit
'Liberating' Firmware from Closed Devices with Open Source…
62 min
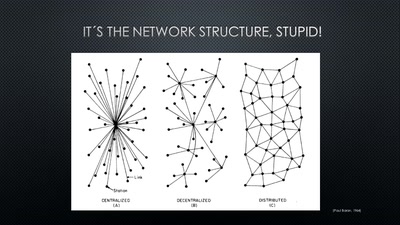
A New Kid on the Block
Conditions for a Successful Market Entry of Decentralized…
60 min
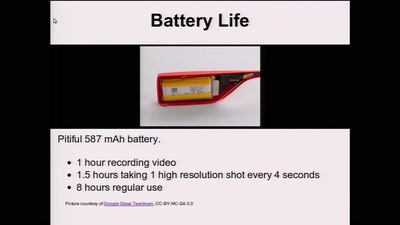
Glass Hacks
Fun and frightening uses of always-on camera enabled…

60 min
From Computation to Consciousness
How computation helps to explain mind, universe and…
59 min
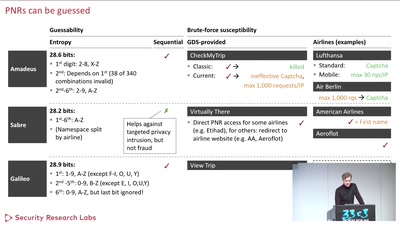
Where in the World Is Carmen Sandiego?
Becoming a secret travel agent
44 min
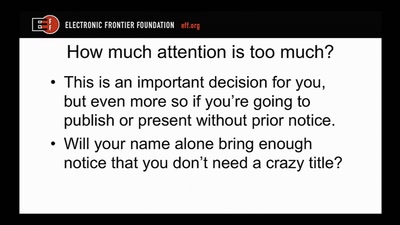
Disclosure DOs, Disclosure DON'Ts
Pragmatic Advice for Security Researchers
54 min
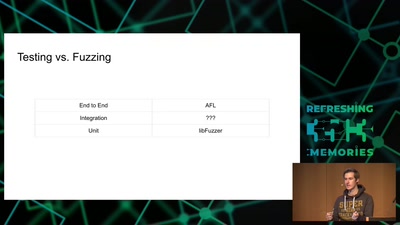
Attacking Chrome IPC
Reliably finding bugs to escape the Chrome sandbox

40 min
What Makes Bike-Sharing Work?
Insights from 43 Million Kilometers of European Cycling Data
36 min
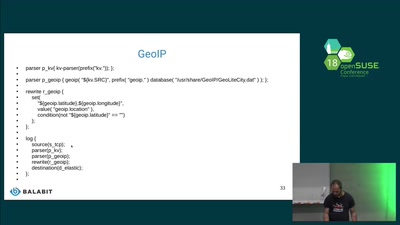
Logging containers
Collecting host, docker and container logs centrally

61 min
wallet.fail
Hacking the most popular cryptocurrency hardware wallets

34 min
Scuttlebutt
The decentralized P2P gossip protocol
63 min
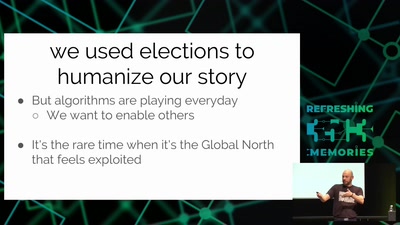
Analyze the Facebook algorithm and reclaim data sovereignty
Algorithms define your priorities. Who else besides you can…
45 min
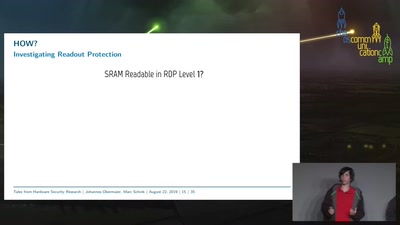
Tales from Hardware Security Research
From Research over Vulnerability Discovery to Public…
43 min
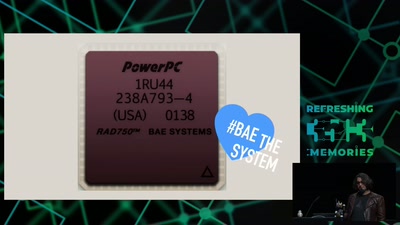
The Mars Rover On-board Computer
How Curiosity's Onboard Computer works, and what you can…
58 min
Protecting Your Privacy at the Border
Traveling with Digital Devices in the Golden Age of…
63 min
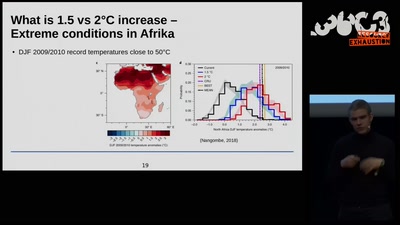
Science for future?
What we can and need to change to keep climate change low -…

58 min