Search for "crypto" returned 406 results

37 min
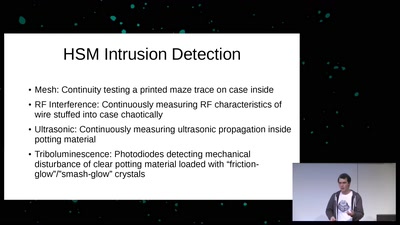
Hacking (with) a TPM
Don't ask what you can do for TPMs, Ask what TPMs can do…
59 min
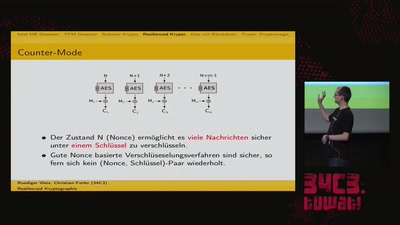
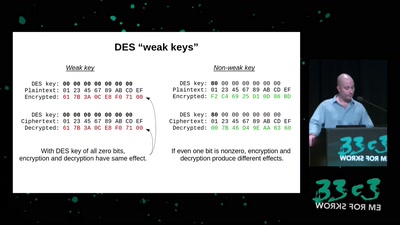
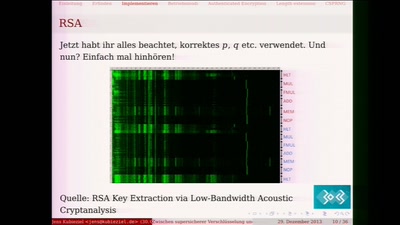
Zwischen supersicherer Verschlüsselung und Klartext liegt nur ein falsches Bit
Ein Streifzug durch die Fehler in der Kryptografie
59 min
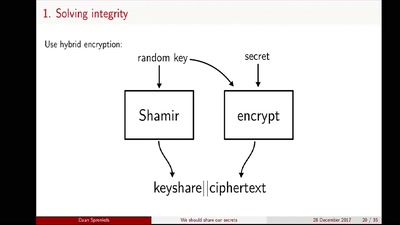
We should share our secrets
Shamir secret sharing: How it works and how to implement it
60 min
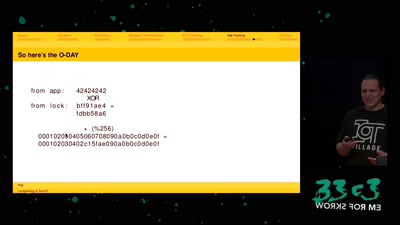
Lockpicking in the IoT
...or why adding BTLE to a device sometimes isn't smart at…
90 min
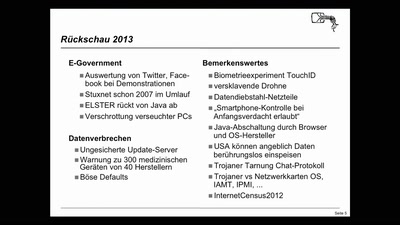
Security Nightmares
Damit Sie auch morgen schlecht von Ihrem Computer träumen.…
61 min
Untrusting the CPU
A proposal for secure computing in an age where we cannot…
58 min
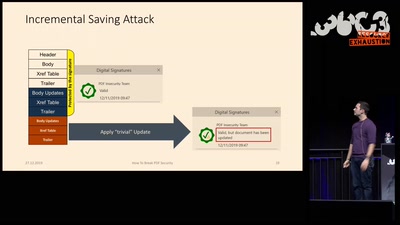
How to Break PDFs
Breaking PDF Encryption and PDF Signatures

38 min
The impact of quantum computers in cybersecurity
Estimating the costs of algorithms for attacks and defense…
55 min
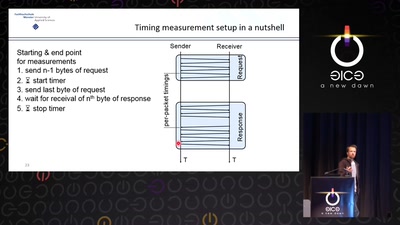
Revisiting SSL/TLS Implementations
New Bleichenbacher Side Channels and Attacks
63 min
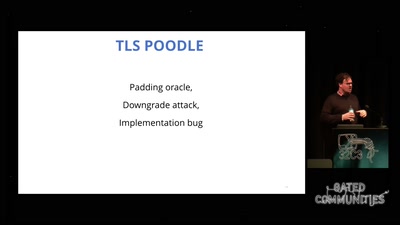
goto fail;
exploring two decades of transport layer insecurity
55 min
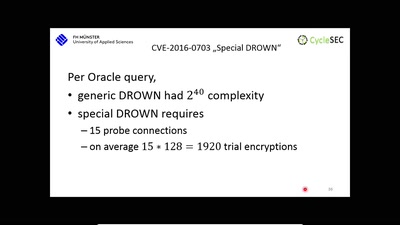
The DROWN Attack
Breaking TLS using SSLv2
41 min
Why Railway Is Safe But Not Secure
Security Of Railway Communication Protocols
19 min
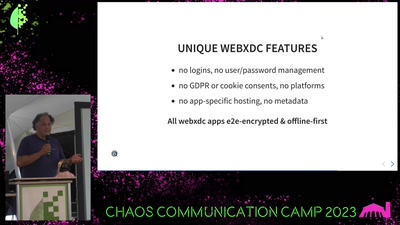
Delta Chat messenger
unlocking the potential of e-mail and the web

41 min
Extracting keys from FPGAs, OTP Tokens and Door Locks
Side-Channel (and other) Attacks in Practice
61 min