Search for "ar3itrary"
prev
next
55 min
Artificial Intelligence Reloaded

36 min
Hardware implants in the supply-chain

32 min
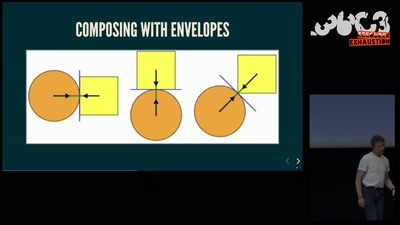
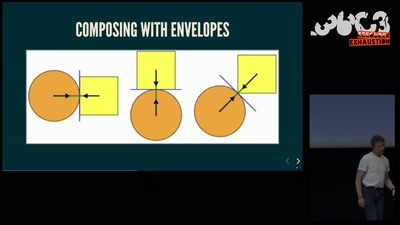
Math, Functional Programming, Theorem Proving, and an…
61 min
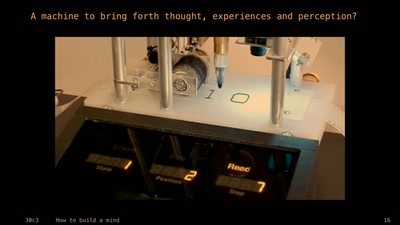
An Artificial Intelligence exploration into the creation of…
66 min
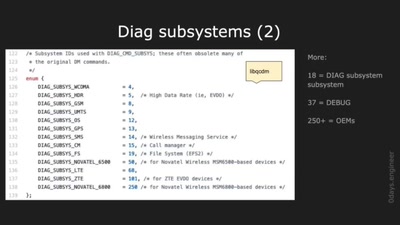
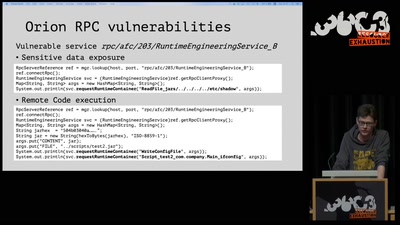
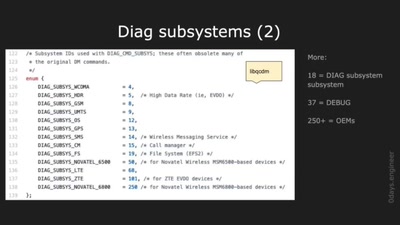
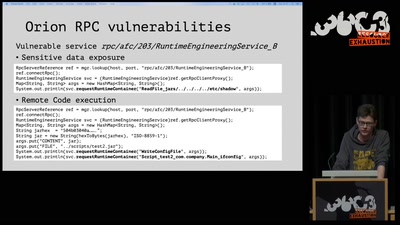
Harnessing diagnostics for baseband vulnerability research
39 min
When your browser is mining coins for other people

57 min
An introduction into reverse-engineering x86 microcode and…
62 min
Evolve your hack into robust software!
29 min
Creating mash-up movies by hidden activity and geography of…
60 min
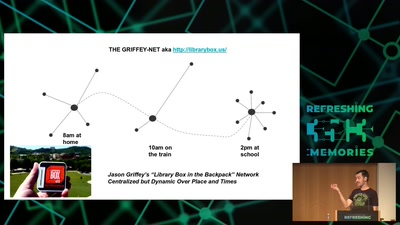
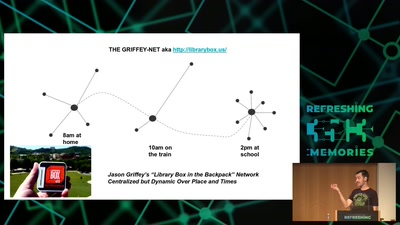
Integrating nearby and offline connectivity with the…
60 min
A security study of turbine control systems in power…
54 min
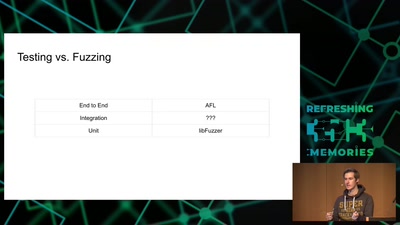
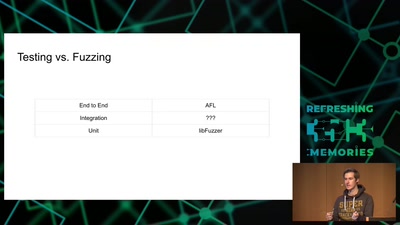
Reliably finding bugs to escape the Chrome sandbox

61 min
fun(ctional) operating system and security protocol…
prev
next