Search for "Nico" returned 1198 results

36 min
Modchips of the State
Hardware implants in the supply-chain
115 min
Vierjahresrückblick des CCC
Nix los und viel zu tun
59 min
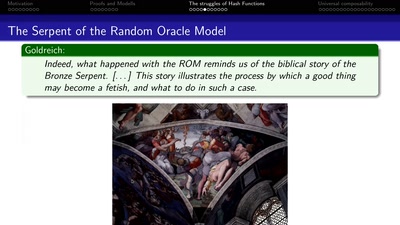
Provable Security
How I learned to stop worrying and love the backdoor
59 min
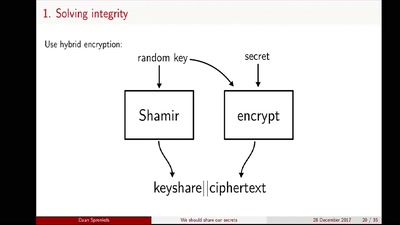
We should share our secrets
Shamir secret sharing: How it works and how to implement it

60 min
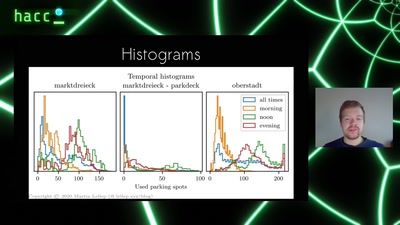
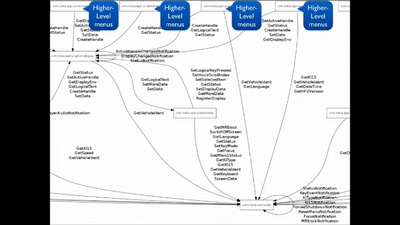
HAL - The Open-Source Hardware Analyzer
A dive into the foundations of hardware reverse engineering…

34 min
Scuttlebutt
The decentralized P2P gossip protocol
26 min
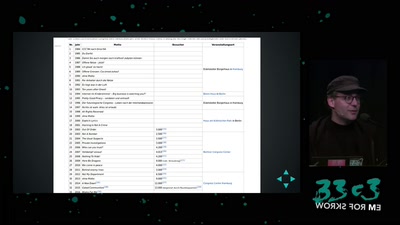
Der 33 Jahrerückblick
Technology and Politics in Congress Talks, from 1984 to now

32 min
Why Do We Anthropomorphize Computers?...
...and dehumanize ourselves in the process?
58 min