Search for "fake" returned 2911 results
41 min
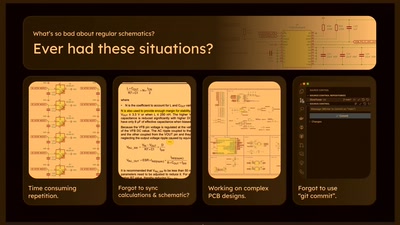
Business Applications as Free Software - Demystifying FUD
You should not believe everything that Big Money tells…
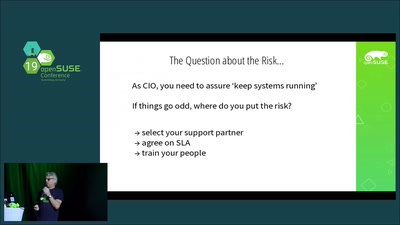
59 min
Safety on the Open Sea
Safe navigation with the aid of an open sea chart.
48 min
3D Printing High-Quality Low-Cost Free Medical Hardware
Making medical devices accessible and hackable for all

56 min
Biohacking in art
An interdisciplinary foray from slime moulds to fungi and…
15 min
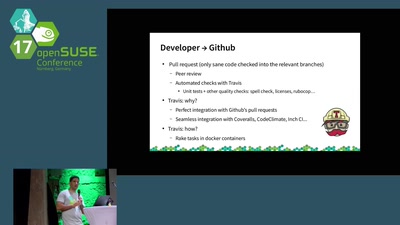
YaST: from the repository to the distributions
Continuous testing and delivery, the YaST way
31 min