Search for "fake" returned 2911 results

59 min
Introducing AI Cockpit
Keep humans in control of AI systems
38 min
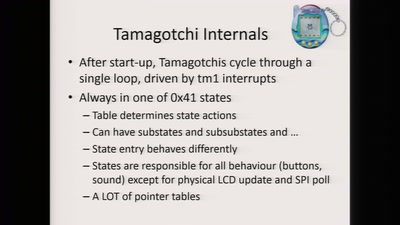
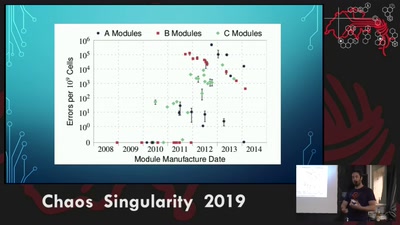
Rowhammer exploit
Viability of the Rowhammer Attack when ECC memory is used
26 min
Don't scan, just ask
A new approach of identifying vulnerable web applications
28 min
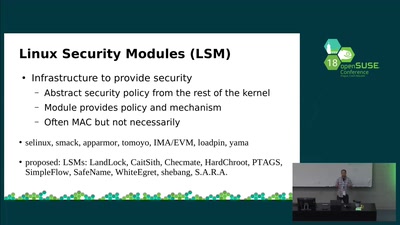
Making the LSM available to containers
stacking and namespacing the LSM
44 min
Legacy Crypto Never Dies
Cracking DES nearly 20 years after the EFF DES Cracker
51 min
Anonymous, secure and easy. You can have them all.
An authentication protocol that offers security, privacy…

50 min