Search for "Lisa" returned 990 results
59 min
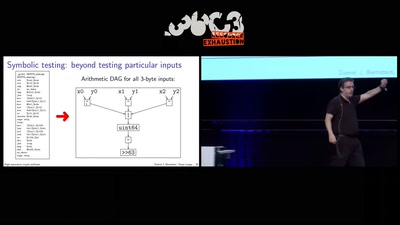
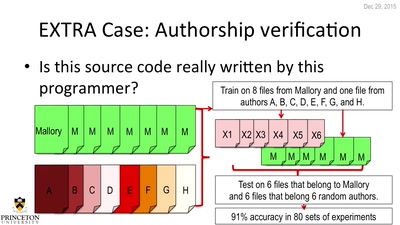
De-anonymizing Programmers
Large Scale Authorship Attribution from Executable Binaries…
60 min
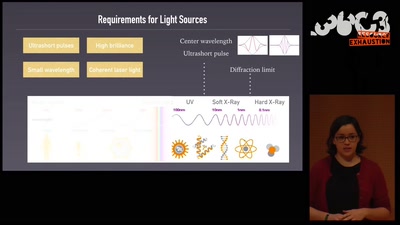
An ultrashort history of ultrafast imaging
Featuring the shortest movies and the largest lasers

61 min
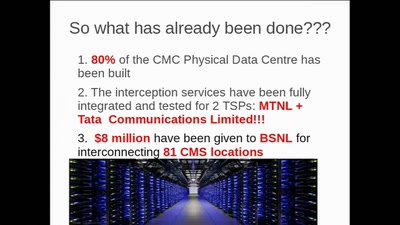
"The" Social Credit System
Why It's Both Better and Worse Than We can Imagine

63 min
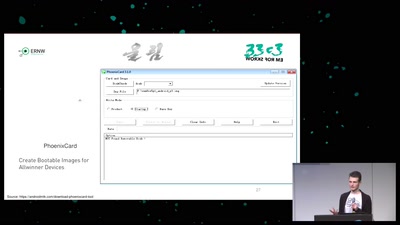
Dissecting HDMI
Developing open, FPGA-based capture hardware for conference…
56 min
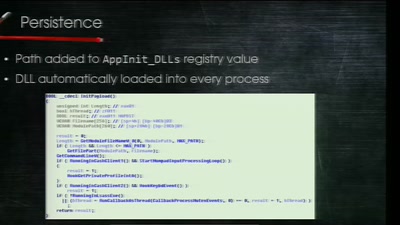
Electronic Bank Robberies
Stealing Money from ATMs with Malware
60 min
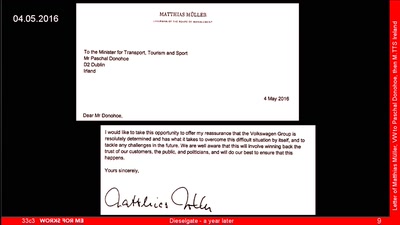
Dieselgate – A year later
env stinks || exit
53 min
When algorithms fail in our personal lives
Social media break up coordinator
60 min
Check your privileges!
How to drop more of your privileges to reduce attack…
63 min
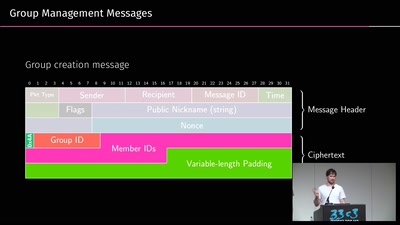
A look into the Mobile Messaging Black Box
A gentle introduction to mobile messaging and subsequent…
58 min
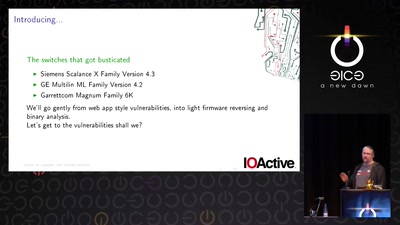
Switches Get Stitches
Industrial System Ownership

41 min
Extracting keys from FPGAs, OTP Tokens and Door Locks
Side-Channel (and other) Attacks in Practice
38 min
A deep dive into the world of DOS viruses
Explaining in detail just how those little COM files…
47 min
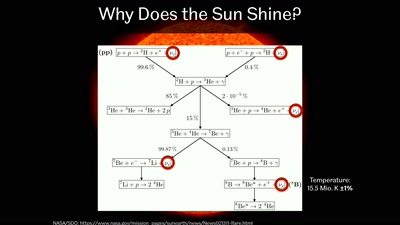
Going Deep Underground to Watch the Stars
Neutrino Astronomy with Hyper-Kamiokande
29 min
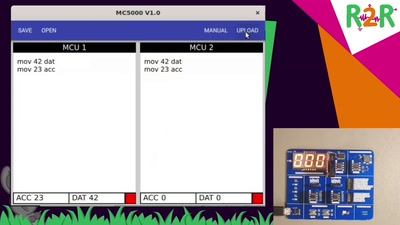
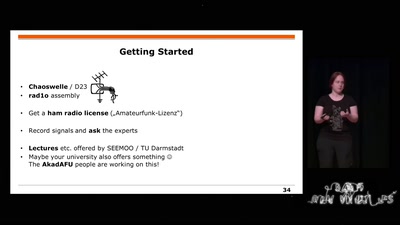
Building and Breaking Wireless Security
Wireless Physical Layer Security & More...
46 min