Search for "OCs of 35C3"
prev
next
55 min
Preserving access to the open Internet with circumvention…

48 min
the superior Multi Factor Authentication Framework

38 min
With the power of open source!

36 min
Hardware implants in the supply-chain
57 min
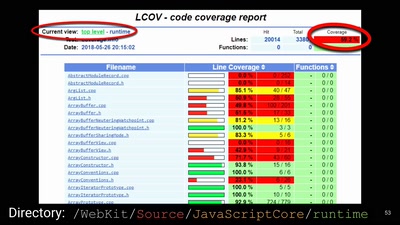
A demystification of the exploit development lifecycle
55 min
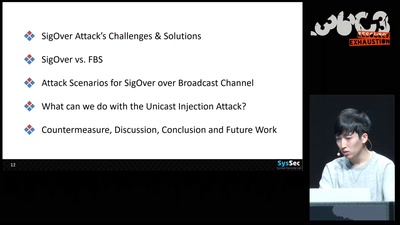
Signal overshadowing attack on LTE and its applications

54 min
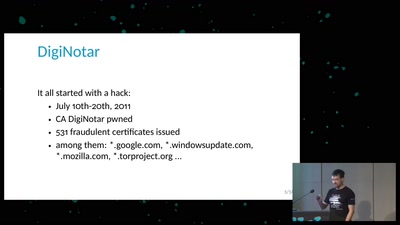
The history and costs of government exceptional access
60 min
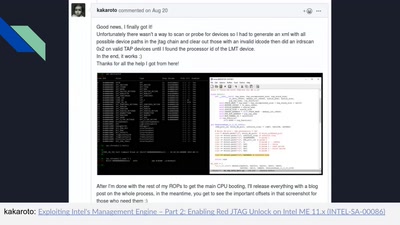
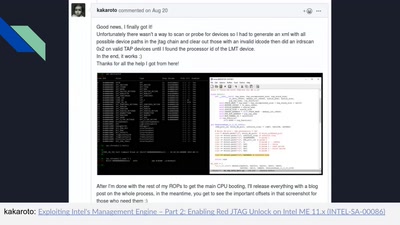
Understanding the ME at the OS and hardware level
58 min
A Historical Re-Enactment of the PayPal14
63 min
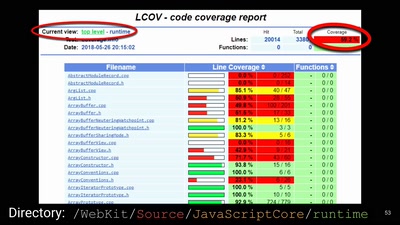
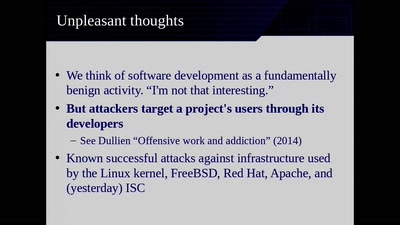
Moving Beyond Single Points of Failure for Software…
prev
next