Search for "Jong-Hoon Lee"
prev
next

58 min
What You Get When Attack iPhones of Researchers
32 min
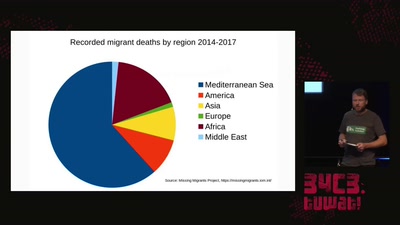
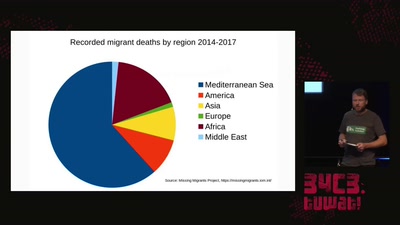
How search and rescue in the mediterranean was criminalized

33 min
the state at the beginning of the 21st Century
49 min
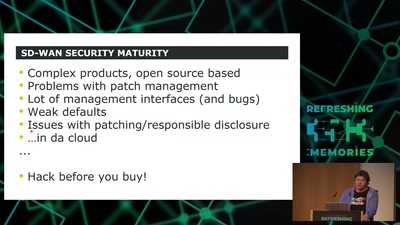
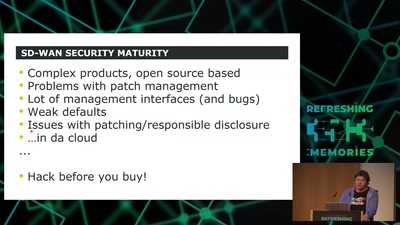
How to hack software defined network and keep your sanity?
40 min
a didactic live-gaming performance about dying women across…
61 min
Let's create the Arduino for FPGAs
61 min
... or how we battle the daemons of memory safety
45 min
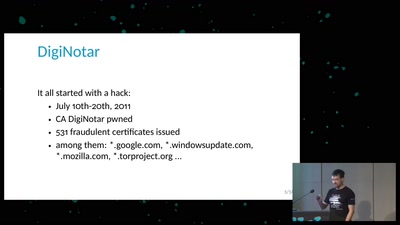
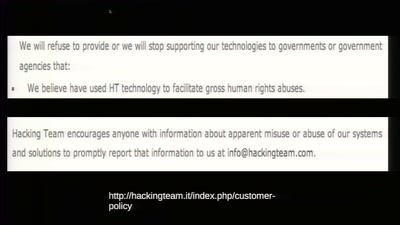
The militarization of the Internet
58 min
CITL: Quantitative, Comparable Software Risk Reporting
64 min
A case for expansionistic space policy

60 min
from key distribution to position-based cryptography
prev
next