Search for "Max" returned 4750 results
39 min
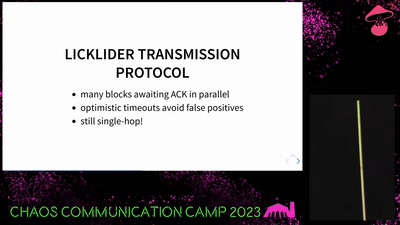
Transmission Control Protocol
TCP/IP basics
55 min
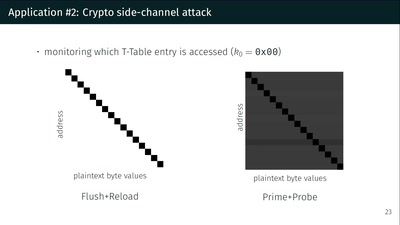
What could possibly go wrong with <insert x86 instruction here>?
Side effects include side-channel attacks and bypassing…
16 min
Decent Patterns
an Open UX Library for Decentralisation
64 min
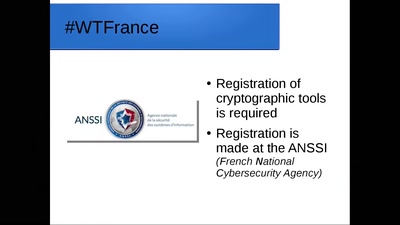
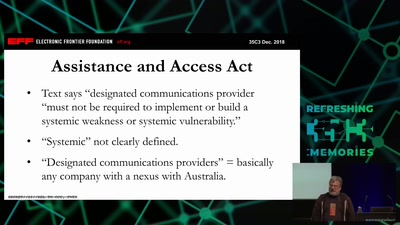
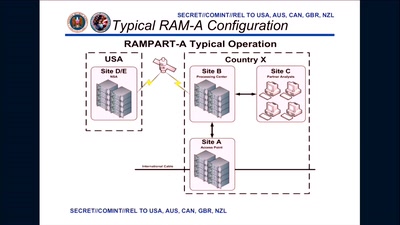
It Always Feels Like the Five Eyes Are Watching You
Five Eyes’ Quest For Security Has Given Us Widespread…
59 min
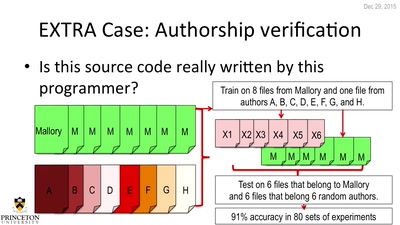
De-anonymizing Programmers
Large Scale Authorship Attribution from Executable Binaries…
30 min
In Search of Evidence-Based IT-Security
IT security is largely a science-free field. This needs to…
57 min
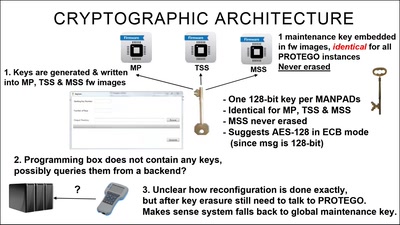
TrustZone-M(eh): Breaking ARMv8-M's security
Hardware attacks on the latest generation of ARM Cortex-M…

14 min
Sharing the power of appreciation
Celebrating 'I Love Free Software Day'

37 min
The foodsaving grassroots movement
How cooperative online structures can facilitate…
64 min
3 Years After Snowden: Is Germany fighting State Surveillance?
A Closer Look at the Political Reactions to Mass…
39 min
The Unfolding Space Glove
A Wearable for the Visually Impaired Translating 3D Vision…

32 min
Verified Firewall Ruleset Verification
Math, Functional Programming, Theorem Proving, and an…
35 min