Search for "Max" returned 4750 results
60 min
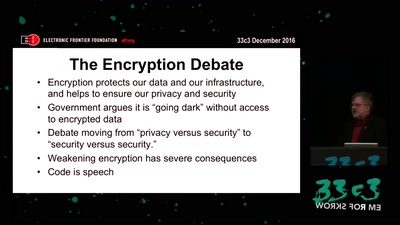
The Fight for Encryption in 2016
Crypto fight in the Wake of Apple v. FBI

32 min
Finding the Weak Crypto Needle in a Byte Haystack
Automatic detection of key-reuse vulnerabilities

61 min
The Invisible Committee Returns with "Fuck Off Google"
Cybernetics, Anti-Terrorism, and the ongoing case against…
53 min
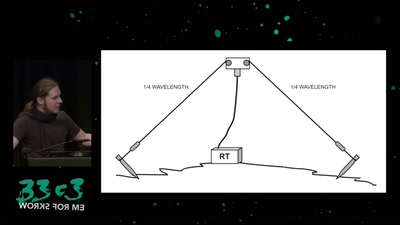
Surveilling the surveillers
About military RF communication surveillance and other…

32 min
Craft, leisure, and end-user innovation
How hacking is conceived in social science research
61 min
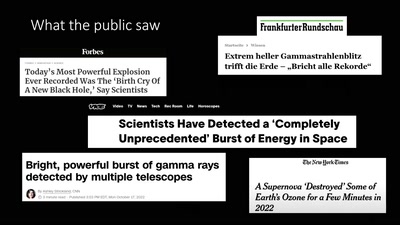
About Gamma-Ray Bursts And Boats
What We (Don't) Know About the Most Energetic Events in the…
60 min
Beyond your cable modem
How not to do DOCSIS networks
63 min
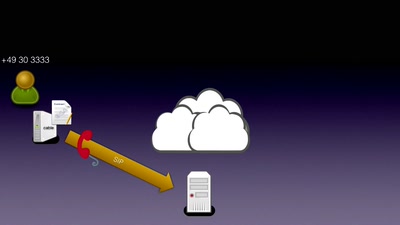
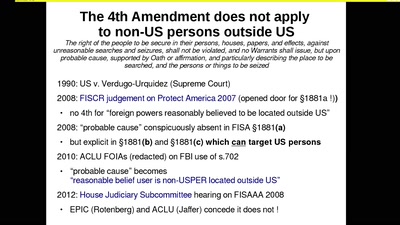
The Cloud Conspiracy 2008-2014
how the EU was hypnotised that the NSA did not exist
57 min
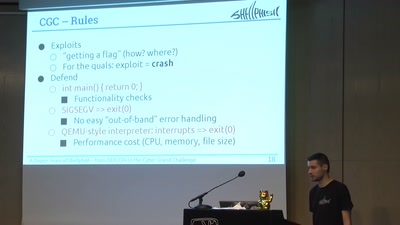
A Dozen Years of Shellphish
From DEFCON to the DARPA Cyber Grand Challenge

41 min
Framing digital industry into planetary limits and transition policies
The environmental costs of digital industry and pathways to…

59 min
Develop Secure Software - The DevGuard Project
OSS Security von Entwicklern für Entwickler
39 min
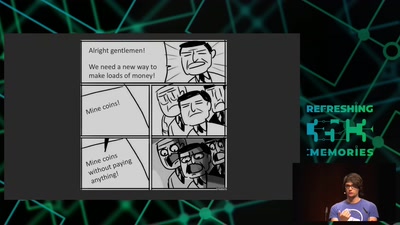
Web-based Cryptojacking in the Wild
When your browser is mining coins for other people
46 min
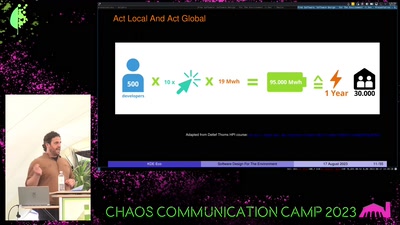
Free Software
Software Design For The Environment
32 min
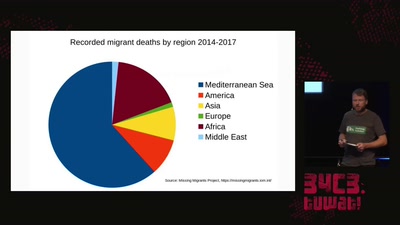
The seizure of the Iuventa
How search and rescue in the mediterranean was criminalized

44 min