Search for "Tom Wills" returned 4761 results
59 min
Fernvale: An Open Hardware and Software Platform, Based on the (nominally) Closed-Source…
A Lawful Method for Converting Closed IP into Open IP
60 min
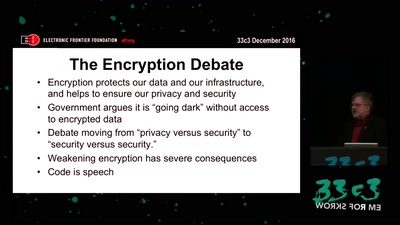
The Fight for Encryption in 2016
Crypto fight in the Wake of Apple v. FBI
61 min
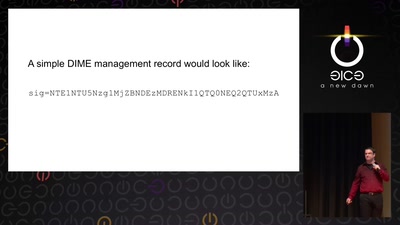
Now I sprinkle thee with crypto dust
Internet reengineering session
59 min
Top X* usability obstacles
*(will be specified later based on usability test with…

67 min
Freude ist nur ein Mangel an Information
Ein Demotivationsworkshop zur politischen Lage.
60 min
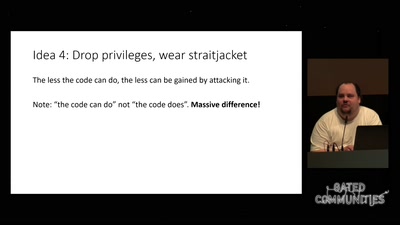
Check your privileges!
How to drop more of your privileges to reduce attack…
62 min
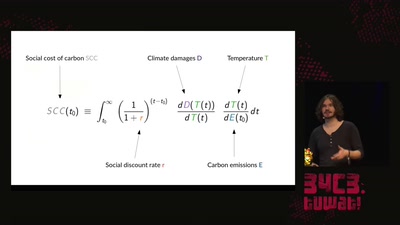
A hacker's guide to Climate Change - What do we know and how do we know it?
An introduction to the basics of climate research and what…
55 min
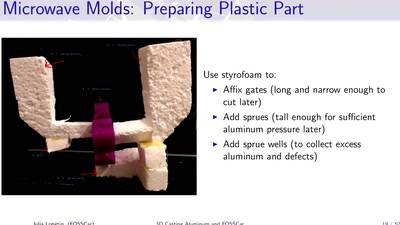
3D Casting Aluminum
Too Much Fun with Microwaves

39 min
Recharge your batteries with us
– an empowering journey through the energy transition
51 min
Virtual Secure Boot
Secure Boot support in qemu, kvm and ovmf.

41 min
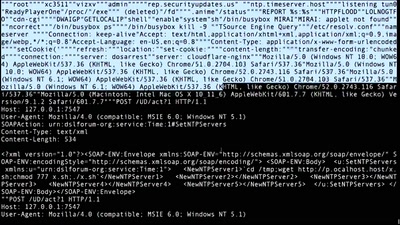
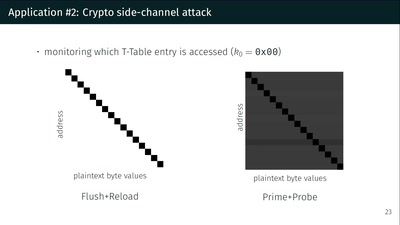
Extracting keys from FPGAs, OTP Tokens and Door Locks
Side-Channel (and other) Attacks in Practice
63 min
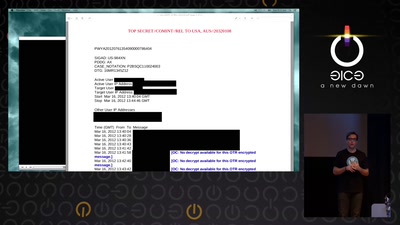
Reconstructing narratives
transparency in the service of justice
61 min
Code Pointer Integrity
... or how we battle the daemons of memory safety

59 min
Security of the IC Backside
The future of IC analysis

44 min
Lützerath Lebt! Einblicke in den Widerstand
Für globale Klimagerechtigkeit kämpfen
60 min
Why is GPG "damn near unusable"?
An overview of usable security research
62 min
radare demystified
after 1.0
55 min