Search for "ari" returned 5363 results

55 min
The Gospel of IRMA
Attribute Based Credentials in Practice
55 min
Our daily job: hacking the law
The key elements of policy hacking
60 min
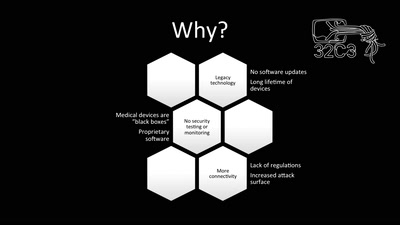
Unpatchable
Living with a vulnerable implanted device
59 min
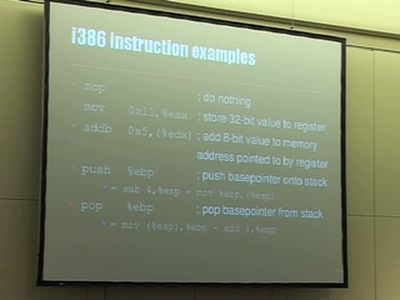
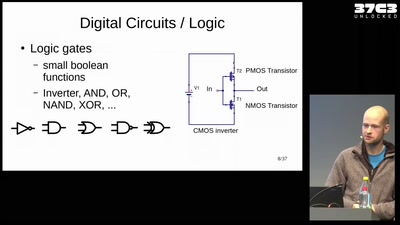
Understanding buffer overflow exploitation
The fascinating interplay of CPU, stack, C-compiler and…
38 min
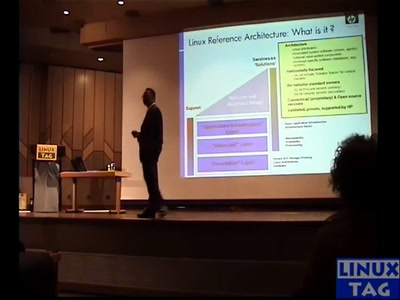
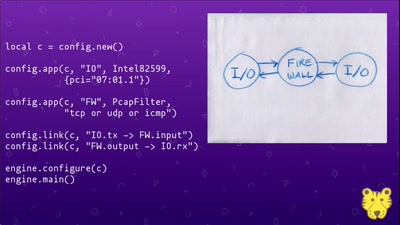
Snabb: fast software networking made simple
A high-performance software toolkit for packet networking…
38 min