Search for "Ari" returned 5376 results

55 min
The Gospel of IRMA
Attribute Based Credentials in Practice
55 min
Our daily job: hacking the law
The key elements of policy hacking
60 min
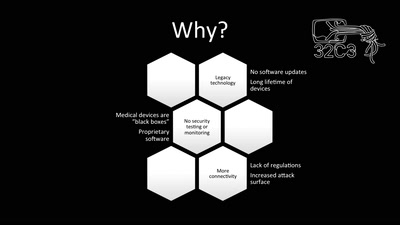
Unpatchable
Living with a vulnerable implanted device
59 min
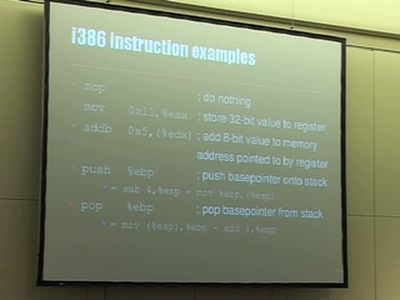
Understanding buffer overflow exploitation
The fascinating interplay of CPU, stack, C-compiler and…
20 min
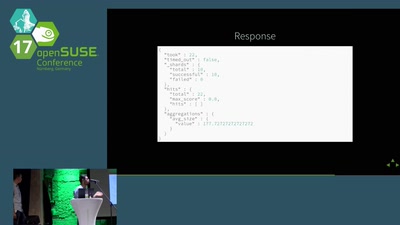
Ceph, ELK & opensuse
This talk will be held by Denys Kondratenko and Abhishek…
57 min
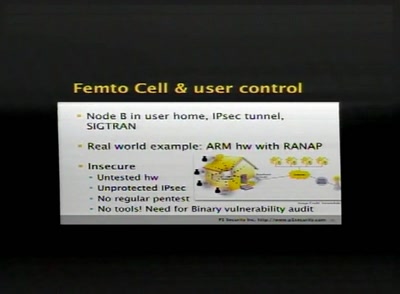
SCCP hacking, attacking the SS7 & SIGTRAN applications one step further and mapping the…
Back to the good old Blue Box?

38 min
On Computable Numbers with an Application to the Modelleisenbahn
Turing Train Terminal

59 min