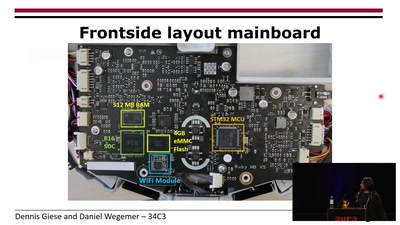
Avatar² is an open source framework for dynamic instrumentation and analysis of binary firmware, which was released in June 2017.
This talk does not only introduce avatar², but also focuses on the motivation and challenges for such a tool.
Dynamic binary instrumentation and analysis are valuable assets for security analysis and testing, and while a variety of tools exist for desktop software, the tooling landscape for analysing low-level binary firmware directly interacting with hardware is relatively empty.
This talk will first outline the key problems for developing dynamic firmware analysis tools and pinpoint different approaches to overcome those problems.
The core of this talk, however, focuses on avatar², an open source framework built to ease firmware reversing and security analysis.
In more detail, avatar² utilizes partial emulation to enable transparent analysis of firmware, and while the main firmware is executed inside the emulator, I/O operations to and from the hardware are commonly relayed to the actual hardware or the emulator. To realize this complex orchestration, avatar² enables communication and state synchronization between a variety of popular tools, such as Qemu, OpenOCD, GDB, PANDA and angr.
While the declared scope of avatar² the is analysis of embedded firmware, this talk will also show that the framework can also be useful in other contexts, such as scripting gdb in python from outside gdb, or loading the state of a concretely executed binary into angr.
Download
Video
These files contain multiple languages.
This Talk was translated into multiple languages. The files available for download contain all languages as separate audio-tracks. Most desktop video players allow you to choose between them.
Please look for "audio tracks" in your desktop video player.