Search for "crypto" returned 406 results
27 min
ANIMAL()CITY
Unleashed!
59 min
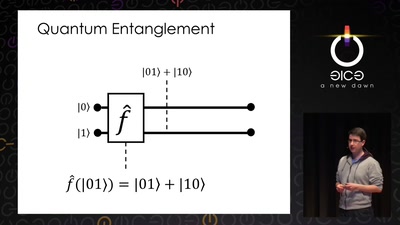
Let's build a quantum computer!
Understanding the architecture of a quantum processor
60 min
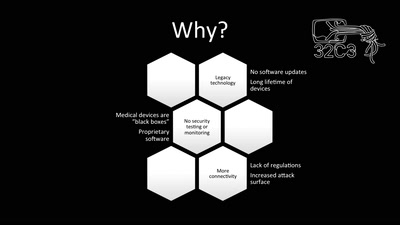
Unpatchable
Living with a vulnerable implanted device
21 min
Welche Sprache sprechen Satelliten?
Ein Überblick über Protokolle und verwendete…

59 min
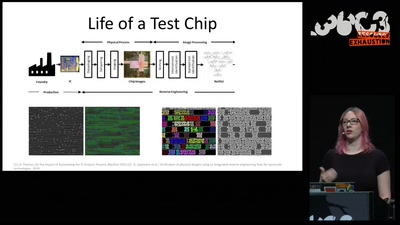
Security of the IC Backside
The future of IC analysis

60 min
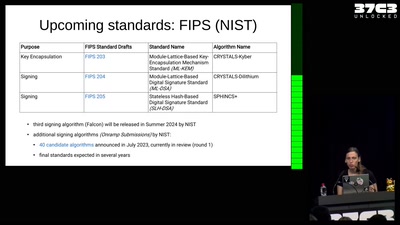
Quantum Cryptography
from key distribution to position-based cryptography
46 min
Writing secure software
using my blog as example
60 min
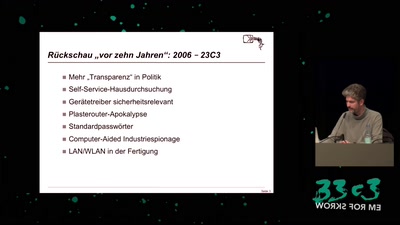
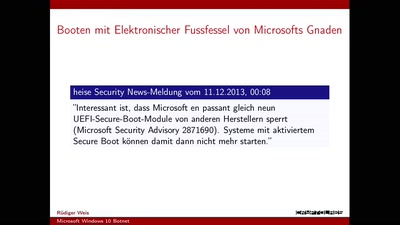
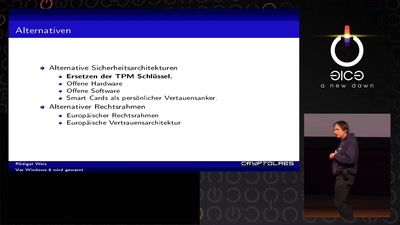
Vor Windows 8 wird gewarnt
Und nichts (Secure) Bootet mehr?

60 min
Attacking end-to-end email encryption
Efail, other attacks and lessons learned.
41 min
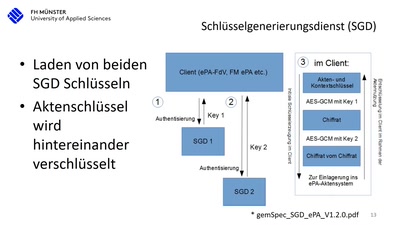
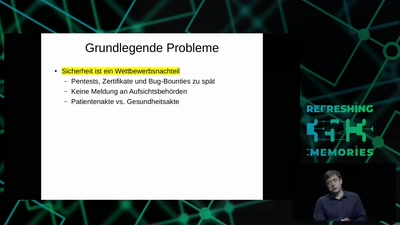
15 Jahre deutsche Telematikinfrastruktur (TI)
Die Realität beim Arztbesuch nach 15 Jahren Entwicklung…
35 min
Understanding millions of gates
Introduction to IC reverse engineering for…
72 min
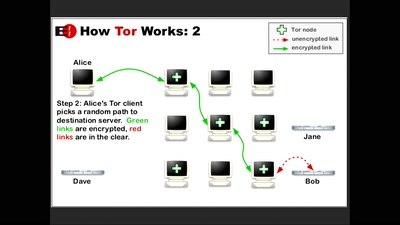
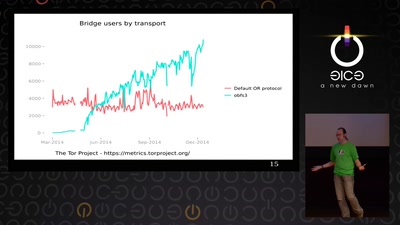
State of the Onion
Neuland
40 min
Fuzz Everything, Everywhere, All at Once
Advanced QEMU-based fuzzing
61 min
All Your Gesundheitsakten Are Belong To Us
"So sicher wie beim Online-Banking": Die elektronische…
26 min
Against Metadata
Twisting time and space to explore the unknown

51 min