Search for "20c3" returned 3928 results

42 min
From Ring Zero to UID Zero
A couple of stories about kernel exploiting

87 min
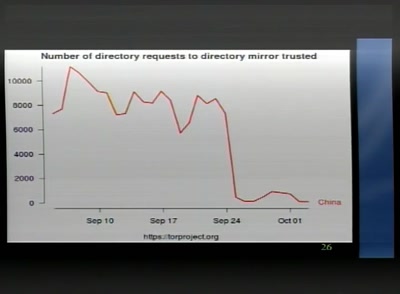
Tor and China
Design of a blocking-resistant anonymity system

59 min
Part-Time Scientists
One year of Rocket Science!
52 min
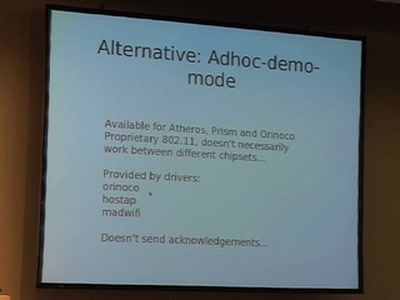
WiFi Long Shots
Wireless connections of 20km and more
46 min
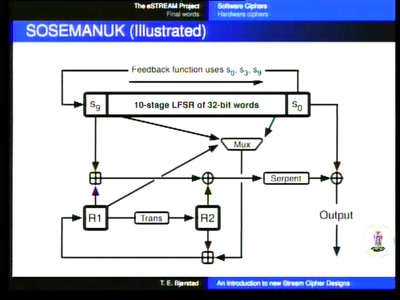
An introduction to new stream cipher designs
Turning data into line noise and back
24 min
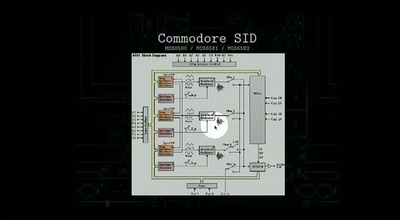
DIY synthesizers and sound generators
Where does the sound come from?
53 min
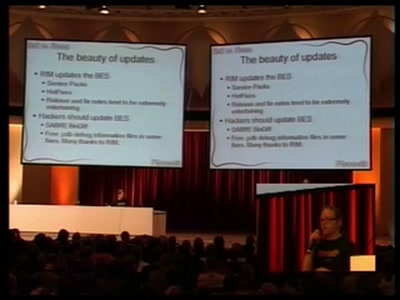
Blackberry: call to arms, some provided
Teach yourself upper management in 22 days

78 min
Stealth malware - can good guys win?
Challenges in detecting system compromises and why we’re so…

26 min
Data Mining the Israeli Census
Insights into a publicly available registry
51 min
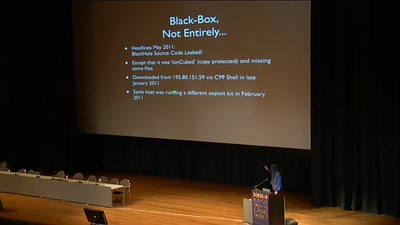
Analytical Summary of the BlackHole Exploit Kit
Almost Everything You Ever Wanted To Know About The…
57 min
How To Design A Decent User Interface
Take a look at software from a user's point of view and…
63 min
Güter und Personen "tracken" - Lokalisierung im Pizzamann-Universum
Technische Mittel und soziale Aspekte des "Tracking &…
59 min
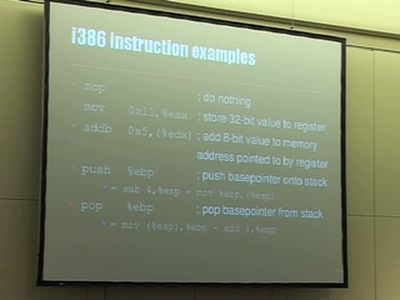
Understanding buffer overflow exploitation
The fascinating interplay of CPU, stack, C-compiler and…

21 min