Search for "INCO" returned 2862 results
61 min
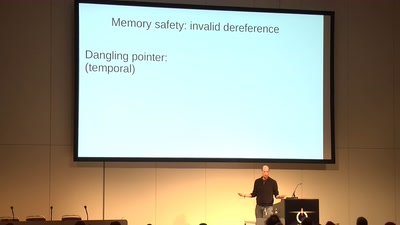
Code Pointer Integrity
... or how we battle the daemons of memory safety

51 min
Funky File Formats
Advanced binary tricks

60 min
Hacking Reality
Mixed Reality and multi-sensory communication

24 min
The Four Wars
Terror, whistleblowers, drugs, internet

61 min
Avoiding kernel panic: Europe’s biggest fails in digital policy-making
How the institutions fuck up, and how we fuck it up as well

41 min
Extracting keys from FPGAs, OTP Tokens and Door Locks
Side-Channel (and other) Attacks in Practice
41 min
Corona-Warn-App
Behind the scenes: Invisible, yet important
54 min
Tactical Embodiment
Activism and Performance In Hostile Spaces Online
33 min
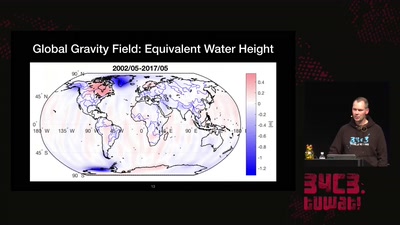
Watching the changing Earth
warning: gravity ahead

64 min
Cory Doctorow – Fireside Chat
Reading and Q&A
60 min
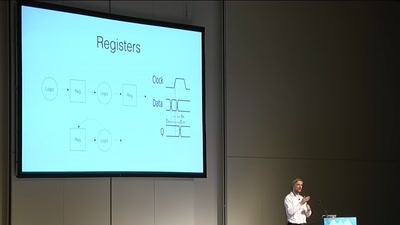
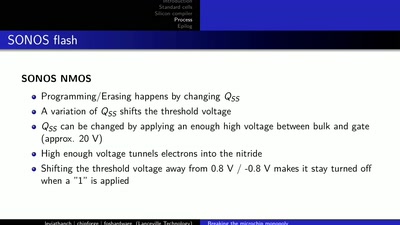
LibreSilicon
Decentralizing semiconductor manufacturing
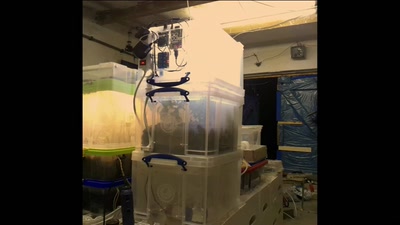
26 min