Search for "crypto" returned 406 results
58 min
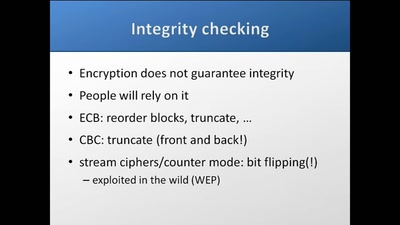
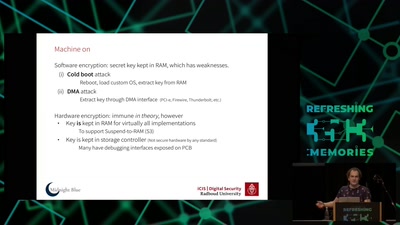
Self-encrypting deception
weaknesses in the encryption of solid state drives (SSDs)
35 min
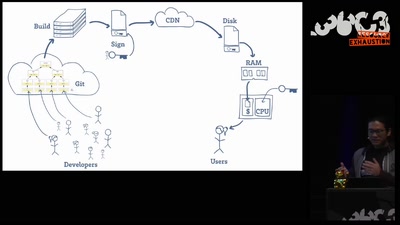
Wallet Security
How (not) to protect private keys
59 min
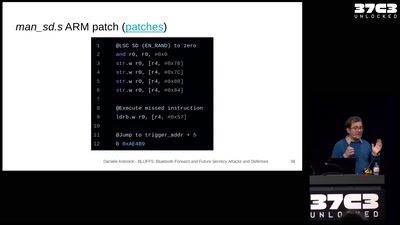
BLUFFS: Bluetooth Forward and Future Secrecy Attacks and Defenses
Breaking and fixing the Bluetooth standard. One More Time.
56 min
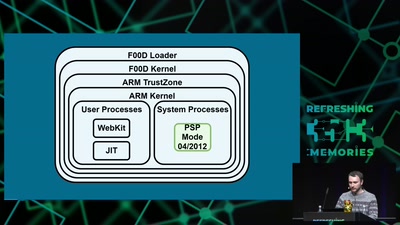
Viva la Vita Vida
Hacking the most secure handheld console

58 min
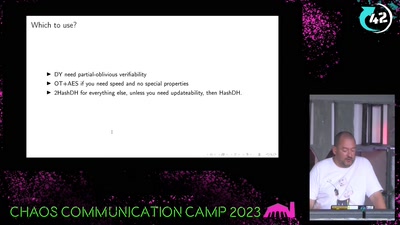
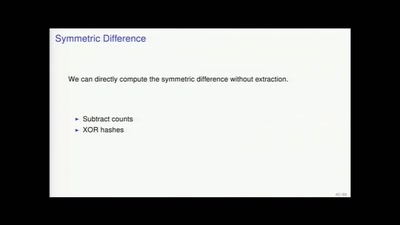
The Magic World of Searchable Symmetric Encryption
A brief introduction to search over encrypted data
60 min
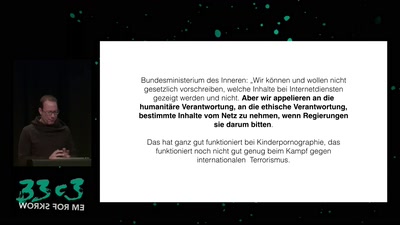
Privatisierung der Rechtsdurchsetzung
Was der Anti-Terror-Kampf von der Urheberrechtsdurchsetzung…
30 min
In Search of Evidence-Based IT-Security
IT security is largely a science-free field. This needs to…
54 min
Do You Think That's Funny?
Art Practice under the Regime of Anti-Terror Legislation
51 min
The GNU Name System
A Decentralized PKI For Social Movements
59 min
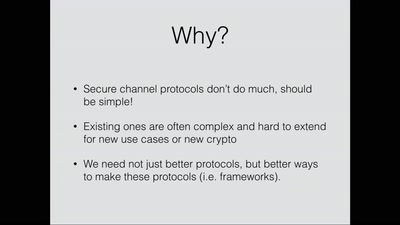
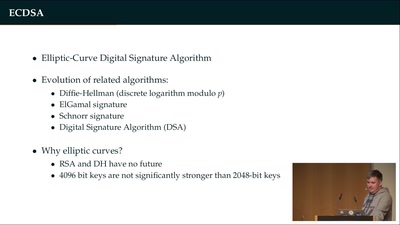
Provable Security
How I learned to stop worrying and love the backdoor
63 min
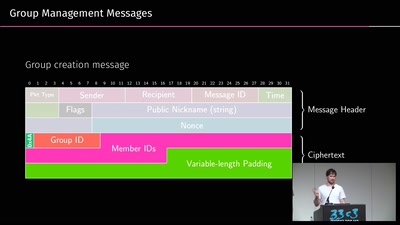
A look into the Mobile Messaging Black Box
A gentle introduction to mobile messaging and subsequent…
47 min
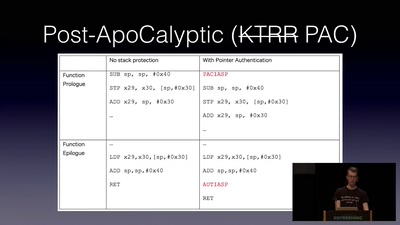
Jailbreaking iOS
From past to present

55 min
The Gospel of IRMA
Attribute Based Credentials in Practice
60 min
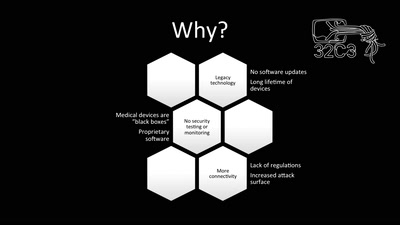
Unpatchable
Living with a vulnerable implanted device
60 min