Search for "CAGE" returned 2972 results

62 min
HUMUS sapiens
Open Soil Research
60 min
APT Reports and OPSEC Evolution, or: These are not the APT reports you are looking for
How advanced threat actors learn and change with innovation…
32 min
Internet of Dongs
A long way to a vibrant future
42 min
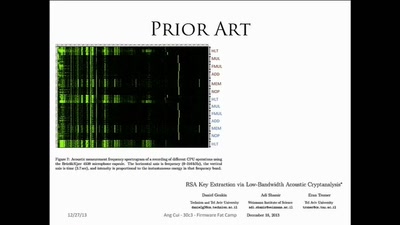
Firmware Fat Camp
Embedded Security Using Binary Autotomy

41 min
Chaos Communication Chemistry
DNA security systems based on molecular randomness

60 min
HAL - The Open-Source Hardware Analyzer
A dive into the foundations of hardware reverse engineering…
46 min
Objects in the Cloud
How object orientation can be used to solve problems in…
63 min
goto fail;
exploring two decades of transport layer insecurity

39 min
Recharge your batteries with us
– an empowering journey through the energy transition
55 min
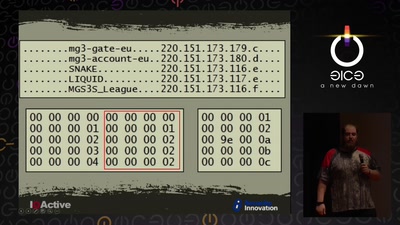
Cyber Necromancy
Reverse Engineering Dead Protocols
40 min