Search for "ultimate" returned 100 results

42 min
Union Busting
What is it and why you should care
60 min
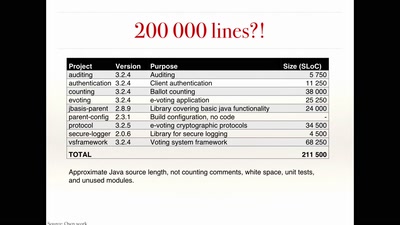
The rise and fall of Internet voting in Norway
Evaluating a complex cryptographic implementation

51 min
How to contribute to make open hardware happen
Mooltipass, Openpandora/Pyra and Novena/Senoko: how I…
60 min
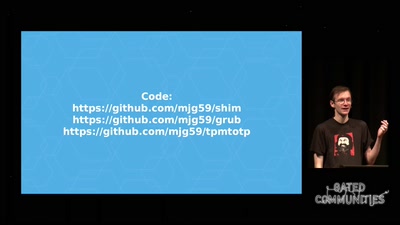
Beyond Anti Evil Maid
Making it easier to avoid low-level compromise, and why…
64 min
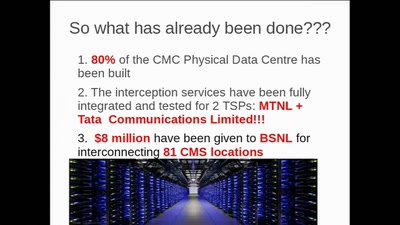
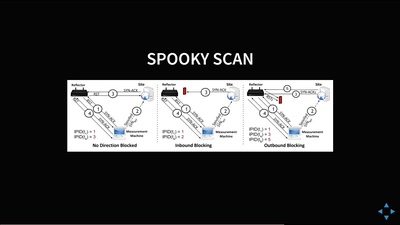
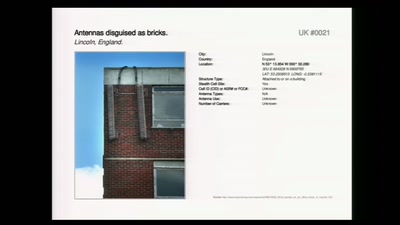
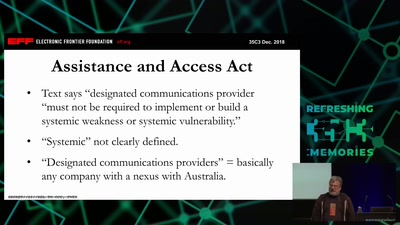
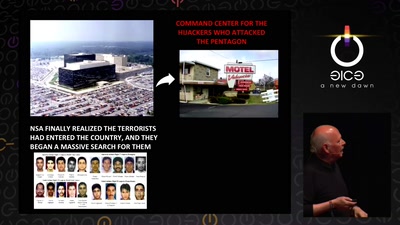
It Always Feels Like the Five Eyes Are Watching You
Five Eyes’ Quest For Security Has Given Us Widespread…

60 min
HAL - The Open-Source Hardware Analyzer
A dive into the foundations of hardware reverse engineering…
53 min
Million Dollar Dissidents and the Rest of Us
Uncovering Nation-State Mobile Espionage in the Wild
61 min
Programming FPGAs with PSHDL
Let's create the Arduino for FPGAs
60 min
Sneaking In Network Security
Enforcing strong network segmentation, without anyone…
54 min
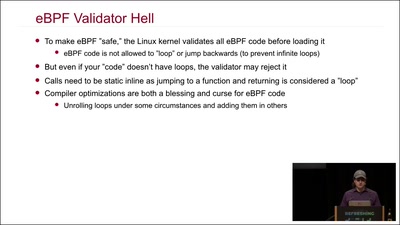
Kernel Tracing With eBPF
Unlocking God Mode on Linux
58 min
Thwarting Evil Maid Attacks
Physically Unclonable Functions for Hardware Tamper…
62 min