Search for "overflo" returned 135 results
43 min
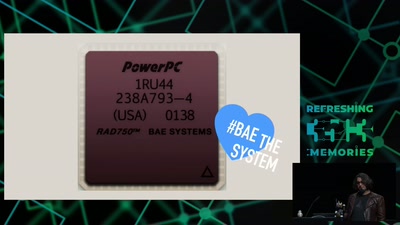
The Mars Rover On-board Computer
How Curiosity's Onboard Computer works, and what you can…
56 min
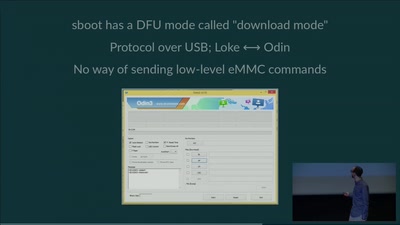
eMMC hacking, or: how I fixed long-dead Galaxy S3 phones
A journey on how to fix broken proprietary hardware by…
59 min
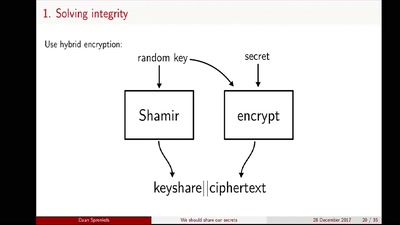
We should share our secrets
Shamir secret sharing: How it works and how to implement it
50 min
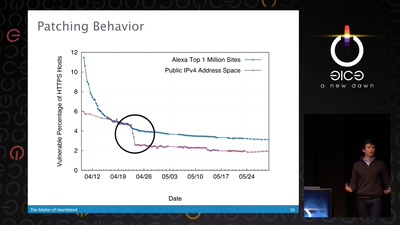
The Matter of Heartbleed
What went wrong, how the Internet reacted, what we can…
46 min
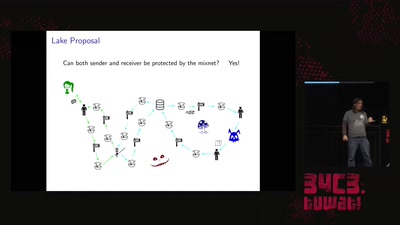
Practical Mix Network Design
Strong metadata protection for asynchronous messaging
30 min
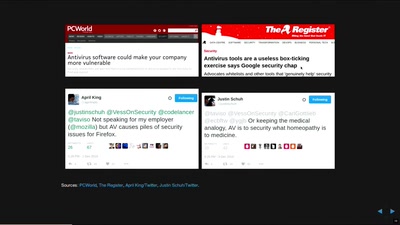
In Search of Evidence-Based IT-Security
IT security is largely a science-free field. This needs to…
36 min
Apple's iPhone 15: Under the C
Hardware hacking tooling for the new iPhone generation
58 min
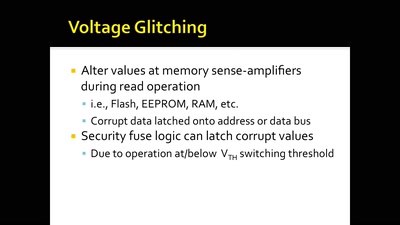
Glitching For n00bs
A Journey to Coax Out Chips' Inner Secrets
38 min
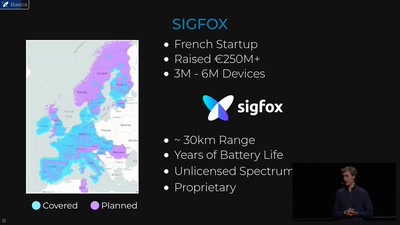
Hunting the Sigfox: Wireless IoT Network Security
Dissecting the radio protocol of Sigfox, the global…
31 min
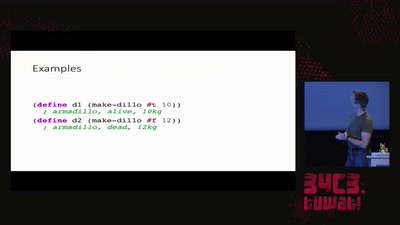
Growing Up Software Development
From Hacker Culture to the Software of the Future

41 min
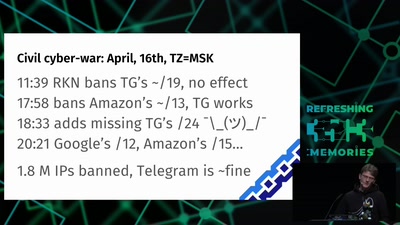
SCADA StrangeLove 2
We already know
60 min
Lets break modern binary code obfuscation
A semantics based approach
47 min
Jailbreaking iOS
From past to present
31 min
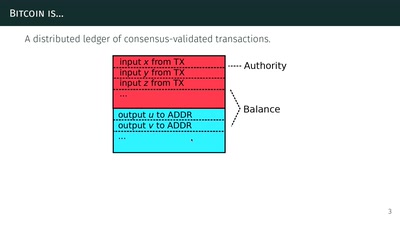
The Zcash anonymous cryptocurrency
or zero-knowledge succinct non-interactive arguments of…
59 min
![Why we are addicted to lithium [1/2]](https://static.media.ccc.de/media/events/rc3/2021/193-3fd1b8af-9ab6-54c5-88ad-2622c1cc925a.jpg)