Search for "cy"
prev
next
39 min
Keeping Secrets On Remote Machines
3 min
A few words by the vice president for research and young…
28 min
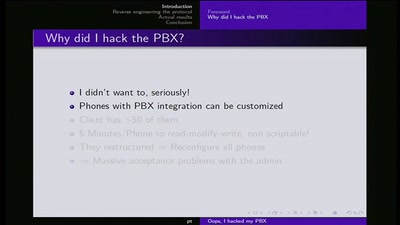
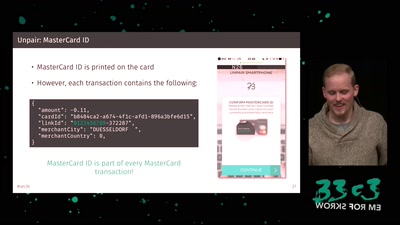
Why auditing proprietary protocols matters
29 min
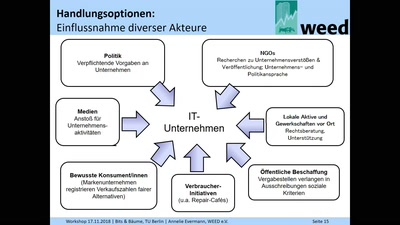
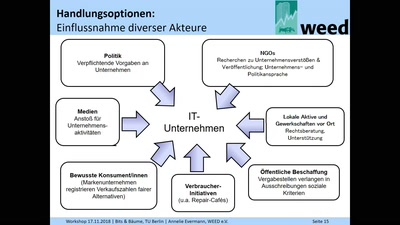
Hintergründe und Handlungsoptionen

57 min
Experiences with Aadhaar in India, or what possibly could…
55 min
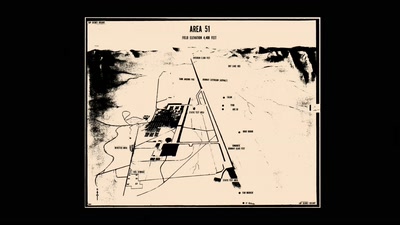
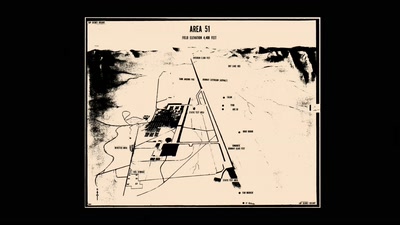
UFOS, MAGIC, MIND CONTROL, ELECTRONIC WARFARE, AI, AND THE…
19 min
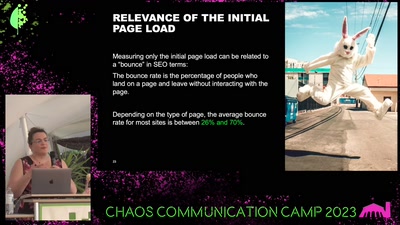
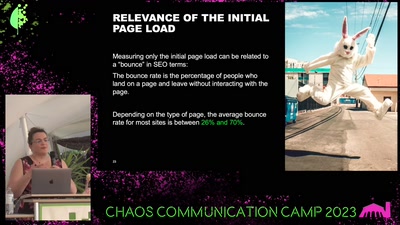
Green Coding & Measuring the Environmental Impacts of IT
30 min
The Red Pill of N26 Security
54 min
Fixing the Multi-million dollar mistake
prev
next