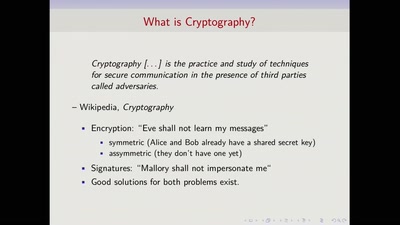
All those shiny cloud services sound tempting, but unfortunately they might mean giving up your private information to someone else. But with modern hardware and crypto, you can have your cake and eat it, too. How does searchable encryption work? What can oblivious RAM protect you from? Where do secure enclaves like Intel SGX shine, and where do they fail? We'll give an overview of how the latest research and products work, how experimental they are, and what they might be used for.
#DeviceSecurity #NetworkSecurity