Search for "Evan Roth" returned 987 results
62 min
Machine Dreams
Dreaming Machines
44 min
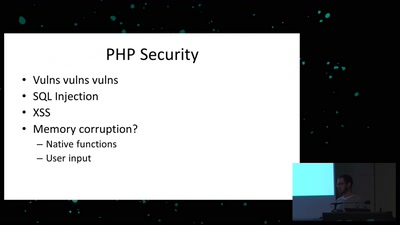
Exploiting PHP7 unserialize
teaching a new dog old tricks
61 min
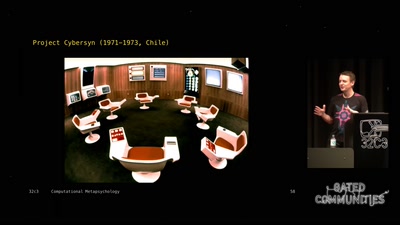
Computational Meta-Psychology
An Artificial Intelligence exploration into the creation of…

59 min
Say hi to your new boss: How algorithms might soon control our lives.
Discrimination and ethics in the data-driven society
64 min
"Exploit" in theater
post-existentialism is the question, not post-privacy
64 min
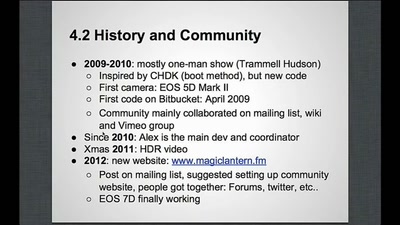
Magic Lantern
Free Software on Your Camera
64 min
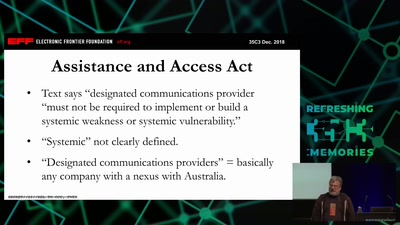
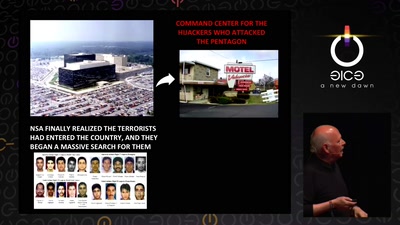
It Always Feels Like the Five Eyes Are Watching You
Five Eyes’ Quest For Security Has Given Us Widespread…

59 min
Security of the IC Backside
The future of IC analysis
35 min
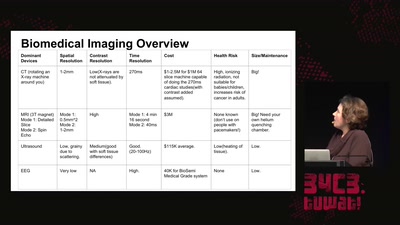
Low Cost Non-Invasive Biomedical Imaging
An Open Electrical Impedance Tomography Project
59 min
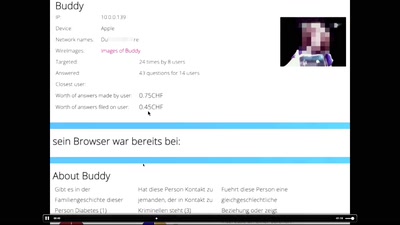
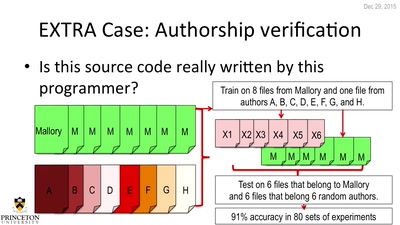
De-anonymizing Programmers
Large Scale Authorship Attribution from Executable Binaries…
56 min
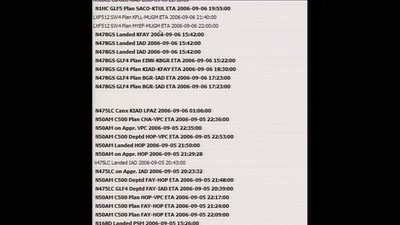
Planes and Ships and Saving Lives
How soft and hardware can play a key role in saving lives…
61 min
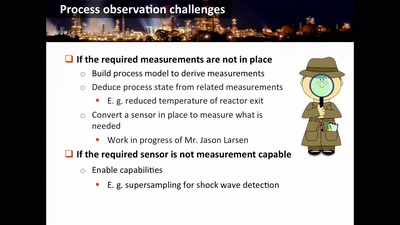
Damn Vulnerable Chemical Process
Exploitation in a new media
62 min
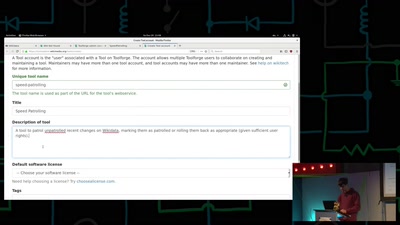
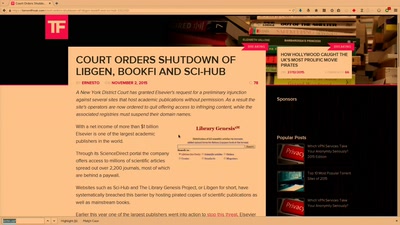
Public Library/Memory of the World
Access to knowledge for every member of society
62 min
Tell no-one
A century of secret deals between the NSA and the telecom…

60 min
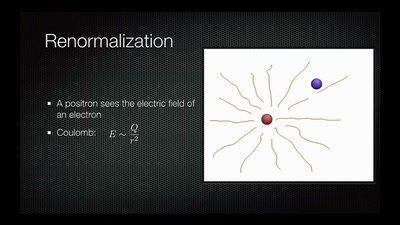
From Computation to Consciousness
How computation helps to explain mind, universe and…
60 min
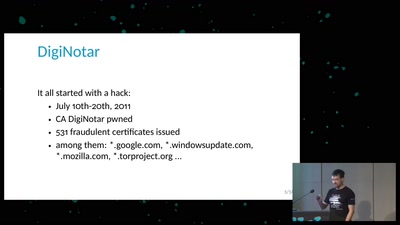
Everything you always wanted to know about Certificate Transparency
(but were afraid to ask)
60 min
Desperately Seeking Susy
A farewell to a bold proposal?
60 min
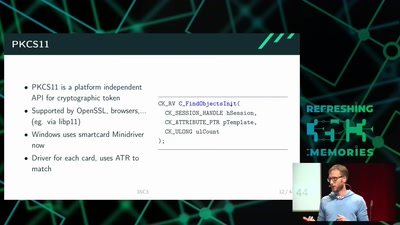
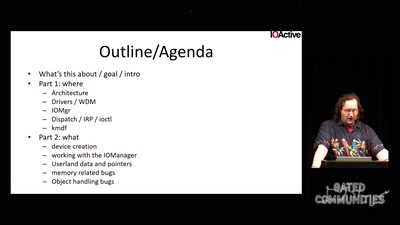
Windows drivers attack surface
some 'new' insights

60 min