Search for "Loic"
prev
next
62 min
Building the First Monero Hardware Wallet
43 min
How to Stop the Dubious Use of Passenger Name Records by…

38 min
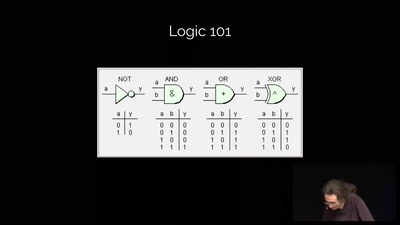
Estimating the costs of algorithms for attacks and defense…

36 min
Hardware implants in the supply-chain
35 min
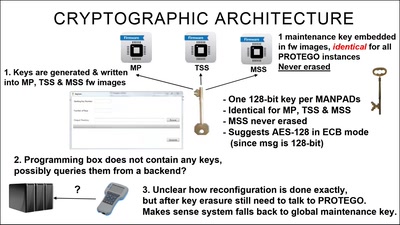
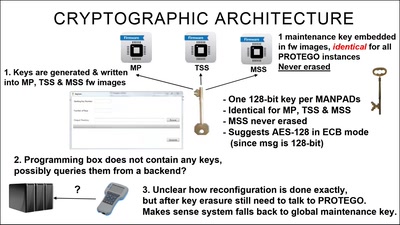
Taking a look at a covert CIA virtual fencing solution
36 min
Hardware hacking tooling for the new iPhone generation
41 min
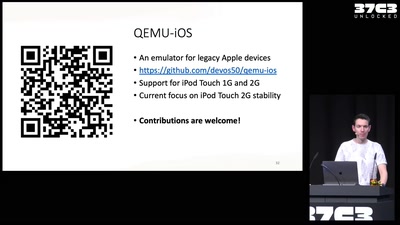
A Dive into Reverse Engineering and Understanding the iPod…

60 min
A dive into the foundations of hardware reverse engineering…
42 min
Dissecting FPGAs from bottom up, extracting schematics and…

46 min
--Gaining code execution using a malicious SQLite database
prev
next