Search for "AKO" returned 1184 results
27 min
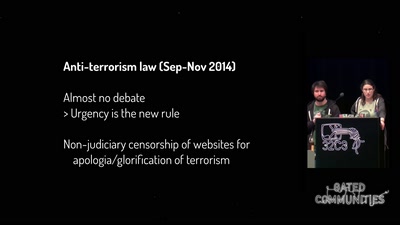
One year of securitarian drift in France
From the Bill on Intelligence to the State of Emergency
46 min
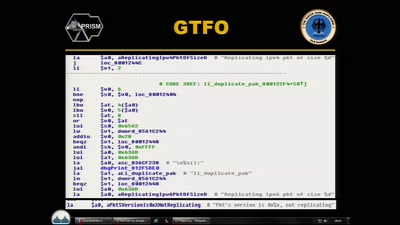
CounterStrike
Lawful Interception

45 min
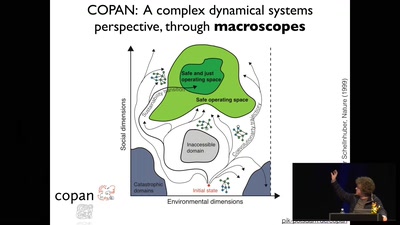
Tech(no)fixes beware!
Spotting (digital) tech fictions as replacement for social…
61 min
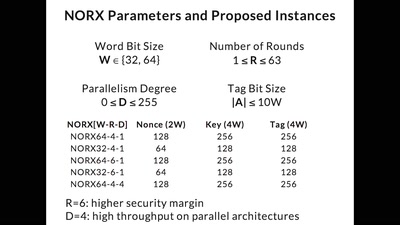
CAESAR and NORX
Developing the Future of Authenticated Encryption
31 min
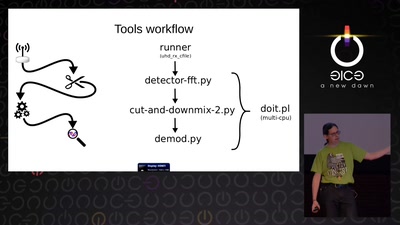
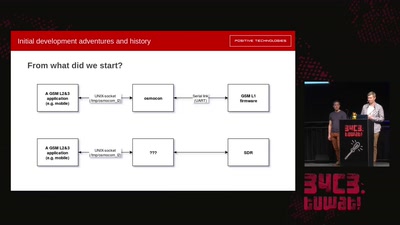
Running GSM mobile phone on SDR
SDR PHY for OsmocomBB
60 min
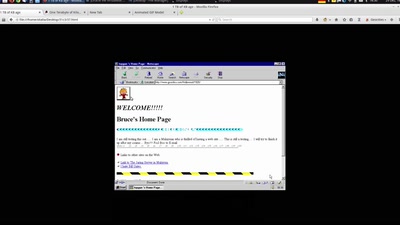
The Only Thing We Know About Cyberspace Is That Its 640x480
One Terabyte of Kilobyte Age
64 min
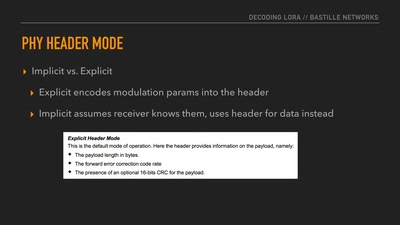
Decoding the LoRa PHY
Dissecting a Modern Wireless Network for the Internet of…

51 min
Funky File Formats
Advanced binary tricks
37 min
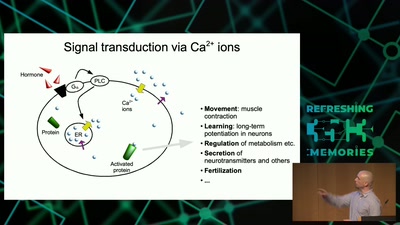
Information Biology - Investigating the information flow in living systems
From cells to dynamic models of biochemical pathways and …
63 min
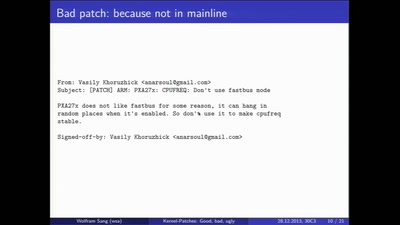
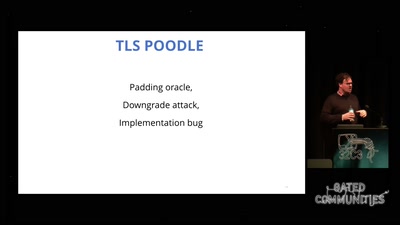
goto fail;
exploring two decades of transport layer insecurity
45 min
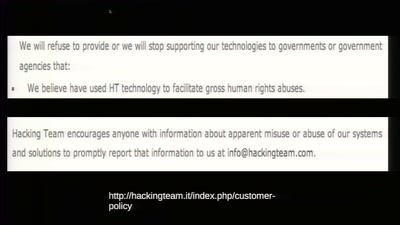
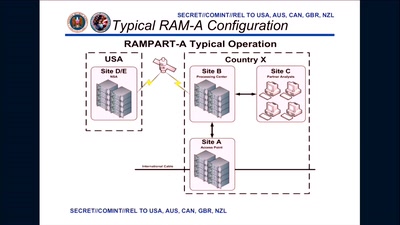
To Protect And Infect
The militarization of the Internet
41 min
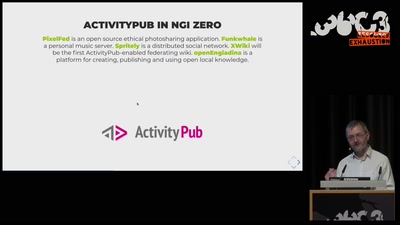
NGI Zero: A treasure trove of IT innovation
Resilient. Trustworthy. Sustainably Open.
60 min
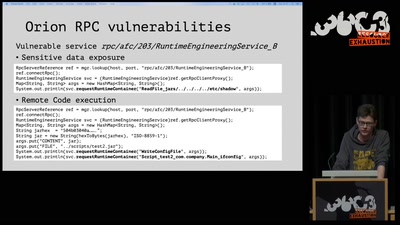
On the insecure nature of turbine control systems in power generation
A security study of turbine control systems in power…
64 min
3 Years After Snowden: Is Germany fighting State Surveillance?
A Closer Look at the Political Reactions to Mass…

60 min