Search for "Victor van der Veen" returned 181 results
53 min
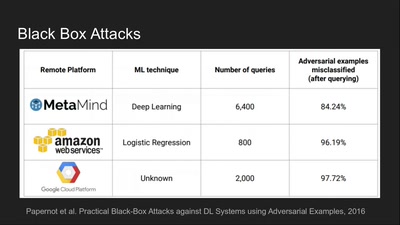
Deep Learning Blindspots
Tools for Fooling the "Black Box"
63 min
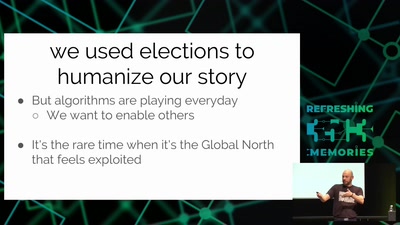
Analyze the Facebook algorithm and reclaim data sovereignty
Algorithms define your priorities. Who else besides you can…
43 min
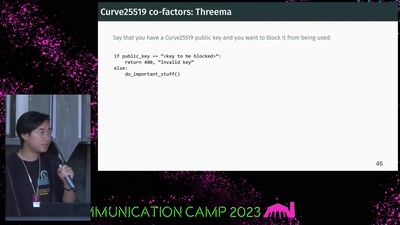
If It Ain't Broken, Do Fix It
Building Modern Cryptography

60 min
Quantum Cryptography
from key distribution to position-based cryptography
62 min
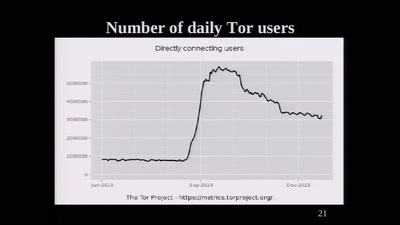
The Tor Network
We're living in interesting times
60 min
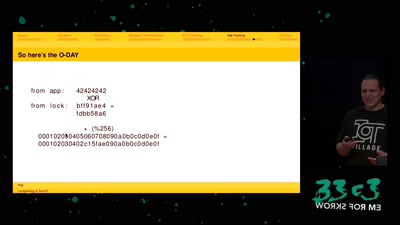
Lockpicking in the IoT
...or why adding BTLE to a device sometimes isn't smart at…

20 min
Mastering the Maze
Unleashing Reinforcement Learning in Penetration Testing…
37 min
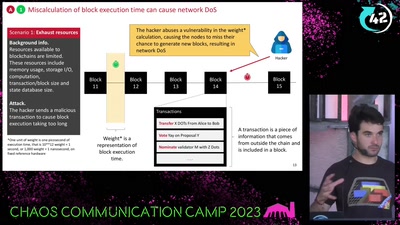
DON’T PANIC
bytes, blocks, bugs

53 min
No Love for the US Gov.
Why Lauri Love’s case is even more important than you…
39 min
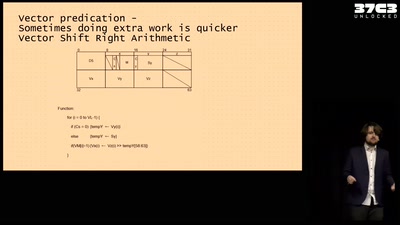
Making homebrew for your very own Vector Super Computer
Adventures running a NEC Vector Engine for fun and ...…

57 min
Everything you want to know about x86 microcode, but might have been afraid to ask
An introduction into reverse-engineering x86 microcode and…
40 min
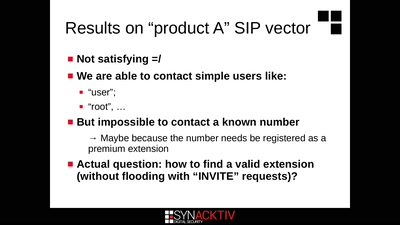
Intercoms Hacking
Call the frontdoor to install your backdoors
61 min
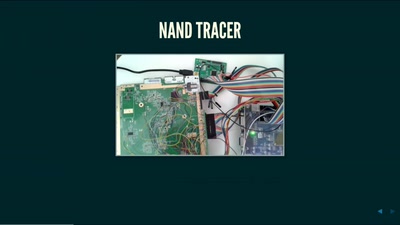
Nintendo Hacking 2016
Game Over
53 min
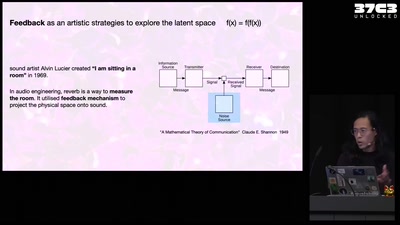
Self-cannibalizing AI
Artistic Strategies to expose generative text-to-image…
63 min
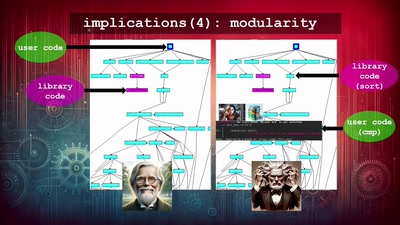
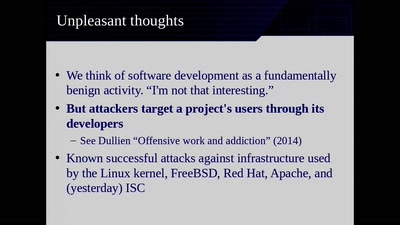
Reproducible Builds
Moving Beyond Single Points of Failure for Software…

51 min