Search for "%s" returned 12406 results

46 min
SELECT code_execution FROM * USING SQLite;
--Gaining code execution using a malicious SQLite database

51 min
Funky File Formats
Advanced binary tricks

26 min
Humans as software extensions
Will You Be My Plugin?
60 min
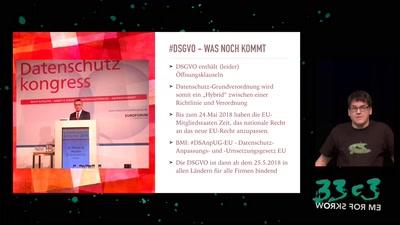
Datenschutzgrundverordnung: Rechte für Menschen, Pflichten für Firmen & Chancen für uns
Schärft das Schwert der Transparenz!

33 min
Gone in 60 Milliseconds
Intrusion and Exfiltration in Server-less Architectures
29 min
2 Takte später
30C3S SCE mbH: GEMA-Konkurrenz für Fortgeschrittene
60 min
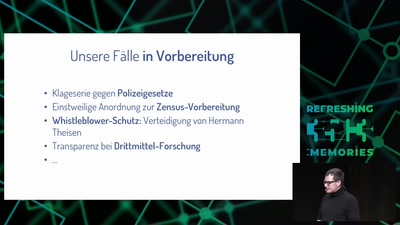
Freedom needs fighters!
Wie die GFF mit strategischen Klagen für Freiheitsrechte…
49 min
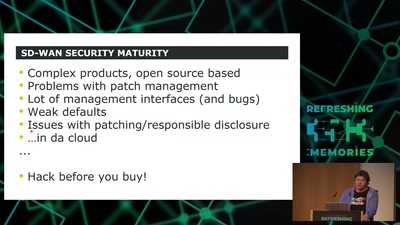
SD-WAN a New Hop
How to hack software defined network and keep your sanity?

32 min
Why Do We Anthropomorphize Computers?...
...and dehumanize ourselves in the process?
63 min
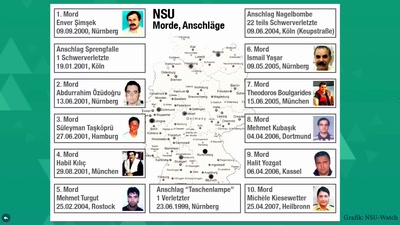
"Das ist mir nicht erinnerlich." − Der NSU-Komplex heute
Fünf Monate nach dem Urteil im ersten NSU-Prozess
31 min
PUFs, protection, privacy, PRNGs
an overview of physically unclonable functions
58 min
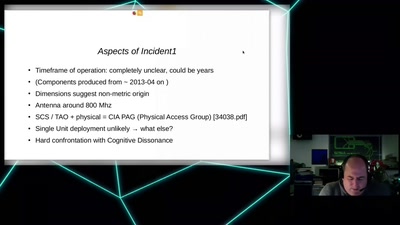
CIA vs. Wikileaks
Intimiditation surveillance and other tactics observed and…

61 min