Search for "tor" returned 10368 results

31 min
Sysadmins of the world, unite!
a call to resistance
41 min
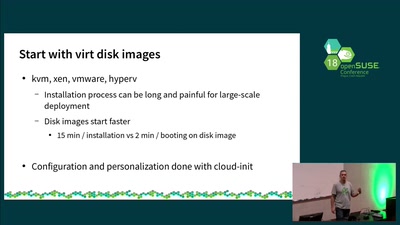
Your first steps with openSUSE Kubic
Practical information on how to get started with openSUSE…
39 min
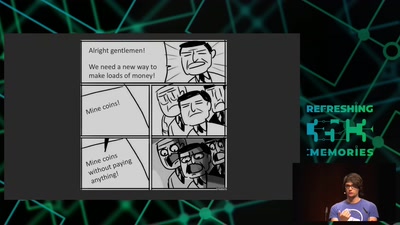
Web-based Cryptojacking in the Wild
When your browser is mining coins for other people
65 min
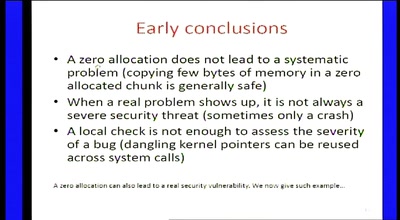
Zero-sized heap allocations vulnerability analysis
Applications of theorem proving for securing the windows…
63 min
Reproducible Builds
Moving Beyond Single Points of Failure for Software…
64 min
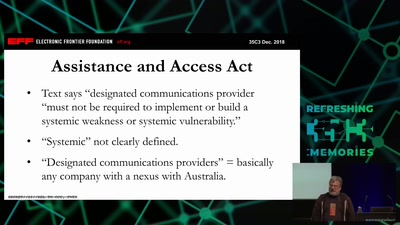
It Always Feels Like the Five Eyes Are Watching You
Five Eyes’ Quest For Security Has Given Us Widespread…

52 min
3G Investigations
Scanning your GPRS/UMTS IP network for fun and profit
58 min
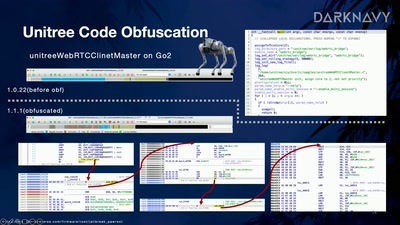
Skynet Starter Kit
From Embodied AI Jailbreak to Remote Takeover of Humanoid…

38 min
All Sorted by Machines of Loving Grace?
"AI", Cybernetics, and Fascism and how to Intervene
37 min
Self-documenting computation
What is the best way to present programs to non-programmers?

59 min
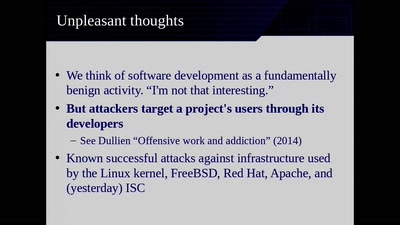
Developments in Coordinated Vulnerability Disclosure
The government is here to help
25 min
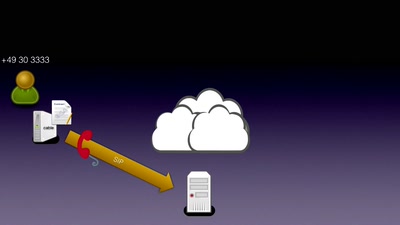
SIP home gateways under fire
Source routing attacks applied to SIP
60 min
Beyond your cable modem
How not to do DOCSIS networks
32 min
History and implications of DRM
From tractors to Web standards

38 min
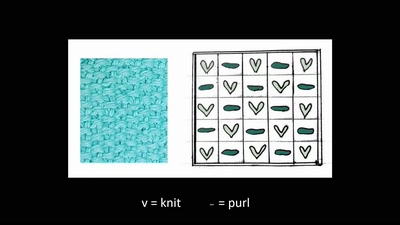
Hardware games
How to build alternative controllers
34 min
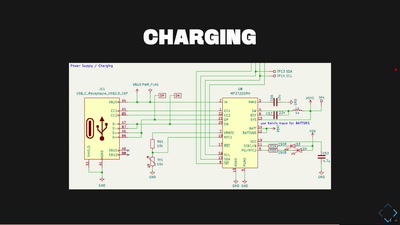
FeTAp 611 unplugged
Taking a rotary dial phone to the mobile age

51 min
Digital Identity and Digital Euro
what is the EU up to now?
58 min
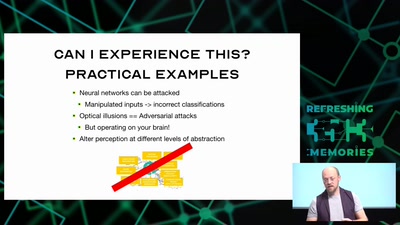
Hacking how we see
A way to fix lazy eye?
23 min
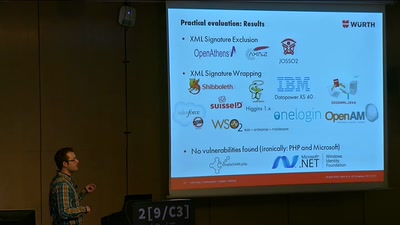
On Breaking SAML
Be Whoever You Want to Be
16 min
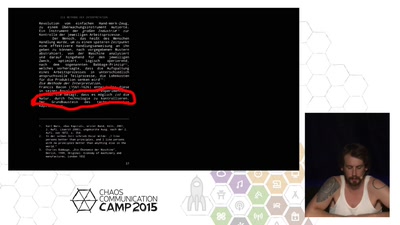
o͈̮p̢ęr̕a͠t̶̨i͟oǹ͓̜a̵l̷ glit̶̨ć̶̛he͝s
How To Make Human Machine Readable

54 min
Singing Capacitors and Whining Inductors
A Practical Introduction to Acoustic Cryptanalysis
58 min