Search for person "Pim van Pelt" returned 114 results

49 min
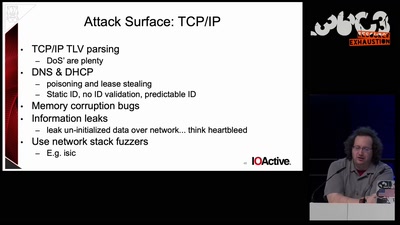
Scanning and reporting vulnerabilities for the whole IPv4 space.
How the Dutch Institute for Vulnerability Disclosure scales…
87 min
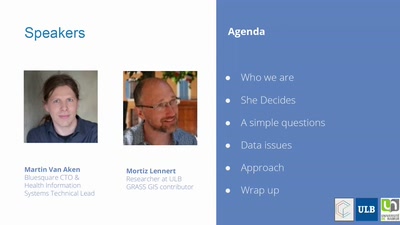
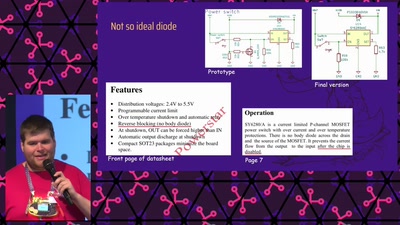
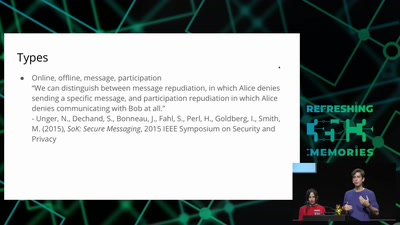
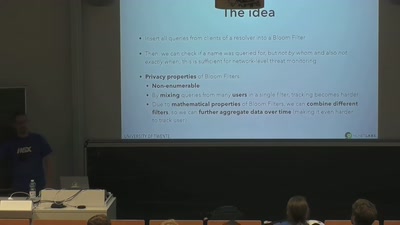
DNS privacy and security
Chaos Colloquium #1

63 min
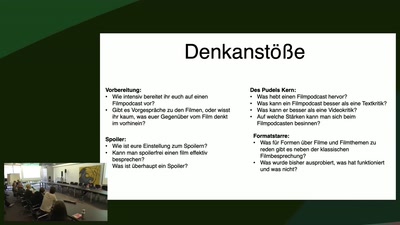
LightKultur in Deutschland
Clubkultur oder wie modern ist unser Kulturbegriff?

25 min