50 min
Console Hacking 2006
Xbox 360, Playstation 3, Wii

72 min
Security Nightmares 2007
Oder: worüber wir nächstes Jahr lachen werden

60 min
Hacking fingerprint recognition systems
Kann ich dir ein Bier ausgeben?
54 min
Building an Open Source PKI using OpenXPKI
Take a lot of Perl, add some OpenSSL, sprinkle it with a…

47 min
How to implement bignum arithmetic
A short look at my pet project implementation

54 min
Unlocking FileVault
An analysis of Apple's encrypted disk storage system

43 min
Nintendo DS
Introduction and hacking

78 min
Stealth malware - can good guys win?
Challenges in detecting system compromises and why we’re so…

34 min
Jabber-Showcase
XMPP ist viel mehr als nur Instant Messaging

68 min
Inside VMware
How VMware, VirtualPC and Parallels actually work
47 min
A not so smart card
How bad security decisions can ruin a debit card design

87 min
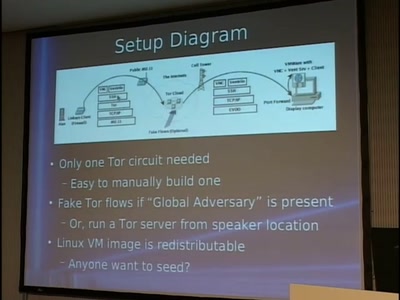
Tor and China
Design of a blocking-resistant anonymity system

55 min
Black Ops 2006 Viz Edition
Pixel Fuzzing and the Bioinformatic Bindiff

69 min
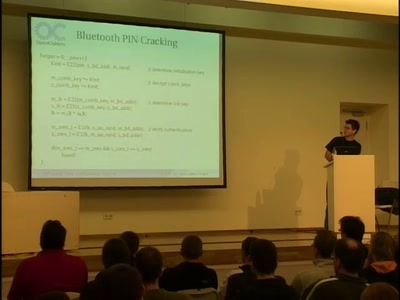
Mobile phone call encryption
Encrypting (GSM) mobile phone calls over VPN with an…

95 min
Analysis of a strong Random Number Generator
by anatomizing Linux' CPRNG

60 min
An Introduction to Traffic Analysis
Attacks, Defences and Public Policy Issues...

46 min
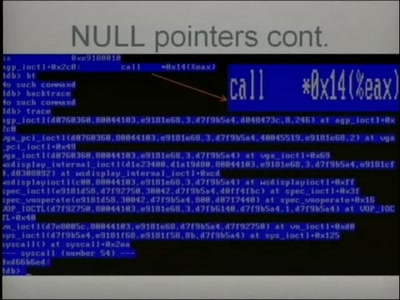
Automated Exploit Detection in Binaries
Finding exploitable vulnerabilities in binaries

45 min
Router and Infrastructure Hacking
"First we take Manhattan, then we take Berlin..."
79 min
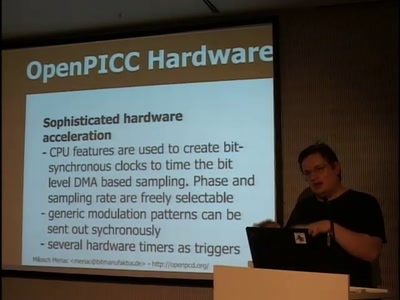
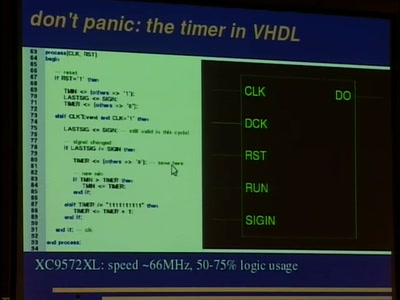
OpenPCD / OpenPICC
Free RFID reader and emulator

49 min
Ethernet mit Mikrocontrollern
Wie funktioniert TCP mit 2kb RAM?
52 min
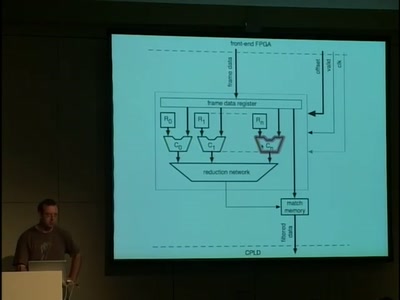
A 10GE monitoring system
Hacking a 10 Gigabit Intrusion detection and prevention…

53 min
Automated Botnet Detection and Mitigation
How to find, invade and kill botnets automated and…

135 min
Project Sputnik
Realtime in-building location tracking at the 23C3

68 min
Software Protection and the TPM
The Mac OS X Story

43 min
Fudging with Firmware
Firmware reverse-engineering tactics

71 min
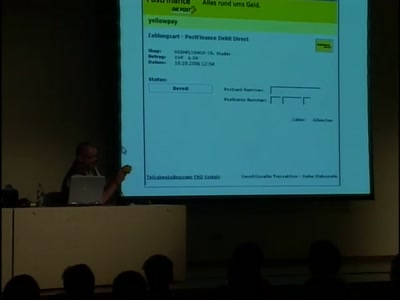
Security in the cardholder data processing?!
Experiences and lessons learned with the Payment Card…
52 min
Void the warranty!
How to start analyzing blackboxes
57 min
How To Design A Decent User Interface
Take a look at software from a user's point of view and…

61 min
Design and Implementation of an object-oriented, secure TCP/IP Stack
Ethereal^W Wireshark without remote exploits - a proof of…

45 min
Introduction to matrix programming: trance codes
How to recognize trance coded communication patterns

63 min
Virtuelle Sicherheit
Mandatory Access Control und TPM in Xen
48 min
Advanced Attacks Against PocketPC Phones
0wnd by an MMS
61 min
CSRF, the Intranet and You
Causes, Attacks and Countermeasures

62 min
Detecting temperature through clock skew
Hot or Not: Defeating anonymity by monitoring clock skew to…
45 min
Secure Network Server Programming on Unix
Techniques and best practices to securely code your network…
50 min
Java wird Groovy
Eine Einführung in die neue, dynamische Sprache für das…
57 min
Software Reliability in Aerospace
An overview on design and generation of safe and reliable…
63 min
Rootkits as Reversing Tools
An Anonymous Talk
53 min
Subverting AJAX
Next generation vulnerabilities in 2.0 Web Applications
60 min