Smart vacuum cleaners as remote wiretapping devices
Exploiting Neato Connected firmware to control high-end vacuum cleaners
The Neato Botvac Connected vacuum cleaners offer a nice platform with up-to-date sensors, including laser scanner mapping your home. The newest Neatos, which are coupled to cloud services over WiFi, run QNX and little was known about them so far. Connected vacuum cleaners are an interesting target regarding privacy, security and safety, as they have access to your home and move freely therein.
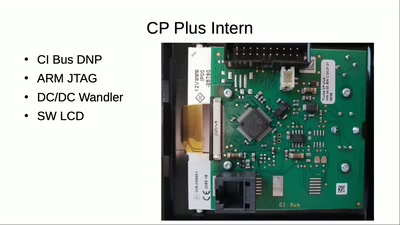
The firmware is protected by a write-only interface and an undocumented chip layout - extracting it is a very interesting process. It is a struggle against proprietary chips and QNX systems. We found an upload serial console, which is their anti brick interface, that only accepts QNX file systems, and guessed the chip family correctly, enabling us to print out some memory contents over the serial console. To actually extract something meaningful from this memory, we performed a regular firmware update process on the robot and rebooted into our modified minimal QNX without re-initializing memory---thereby stealing their complete firmware. Based on the firmware extraction, we found many interesting firmware internals.
We analyzed weak encrypted coredumps produced by the vacuum cleaner during Web interface fuzzing. By this, we identified a buffer overflow vulnerability, which enables remote command execution (RCE) with root privileges on the robot. Our RCE vulnerability works without prior authentication and---before Neato was informed and rolled out a bugfix---executable via their cloud infrastructure by anyone guessing or knowing a robot's serial ID, which is printed on packing and robots. An attacker could leverage the RCE to extract sensitive information from the robot and harm the user's privacy. We explain the vulnerability, our exploit and how we overcame obstacles during proof of concept development.