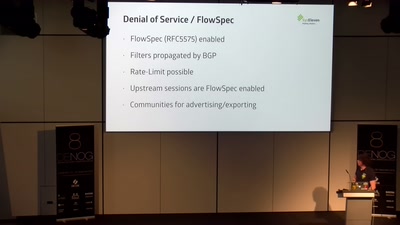
BH (Blackholing) as (very) effective (D)DOS mitigation is nothing new and widely available (will not be further touched). sBH (Selective Blackholing or Regional Blackholing) is also not that new (~2005 outlined by Cisco if not before) but was brought to a wider audience by Job Snijders @ RIPE68 in 2014. Job suggested an implementation in the normal iBGP mesh, which was not an option for us. We roughly outlined on #nlnog how we did it (via dedicated RR) and we are open to share this in more depth with the community. However, any kind of Blackholing is effectively switching of the service; but at the same time protects the rest of ISP's network from suffering by such an attack (overloaded links, too high load on servers). To verify if the attack is over (or to take some traffic samples), the BH needs to be removed ... exposing again ISP's full network to the risk of suffering because of the attack (if still ongoing). Here "RTDCoS" might help. The idea behind RTDCoS (remote triggered destination IP based CoS - or however this will be called in the end) is to allow a downstream to signal via eBGP very simple CoS characteristics to its upstream. This could be (and will be in most cases only) something like "rate-limit all traffic targeted to the tagged prefixes to a (predefined) bandwidth". Even though the techniques used aren't that special, most likely not too many have yet considered of really making use of this. [And then make this eventually regional / selective (with the same reasoning as sBH might be of use) and enable the upstream to use this CoS information not to carry "just all the crap" up to the egress PE where most of it would be discarded anyway.