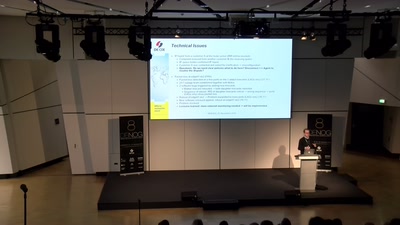
A wide and deep infiltration of a Service Provider and/or its subscribers consists of many smaller process steps by different roles and actors on the criminal side. Do we need different technologies and products to detect and mitigate each criminal actor, role and process step? The Criminal Cloud relies on a functioning Domain Name System (DNS) for the different roles in the Criminal Gang to communicate amongst each other, to reach and infect their next victims, do reconnaissance on new planned targets, command and control botnets and marketing campaigns in the darknet. Above and beyond DNS, Threat Intelligence is a proven tool in identifying, mitigating, remediating and even helping predict the cyber criminal’s next move. By leveraging a combination of DNS based security, Threat Intelligence and collaboration across vendors, many attack vectors can be more effectively prevented, detected, mitigated, and remediated thereby improving security of subscribers and the operator’s network. Participants will get an overview of how Threat Intelligence can complement DNS based protection, why machine learning and entropy analysis are critical for the moving targets in the criminal cloud, why vendor collaboration is key, and what questions to ask the next security vendor that comes knocking on their door.