djb, Jean-Philippe Aumasson and Martin Boßlet
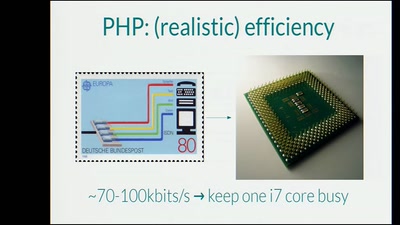
At 28C3, Klink and Waelde showed that a number of technologies (PHP, ASP.NET,
Ruby, Java, Python, etc.) were vulnerable to the decade-old hash-flooding DoS
attacks. The vulnerability was then often fixed by adopting stronger hash
functions and "randomizing" them.